
The Woodruff Institute has several locations in Florida specializing in dermatology and plastic surgery. Unfortunately for them, they appear to have been the victims of threat actors who call themselves “Pay or Grief” (or just “Grief”).
On June 11, the threat actors added the medical practice to their dedicated leak site, and on June 15, they updated the listing, dumping additional data that they claimed to have exfiltrated from the practice’s files.

In an exclusive interview with Suspect File on June 1, a spokesperson for Grief told Marco De Felice that the group would not attack medical entities. But like some other threat groups, they don’t seem to include plastic surgery practices in that exclusion:
We aren’t going to target health sector. We know some players like it, but there are a lot more interesting sectors to make money. Some things like plastic surgery or pharma sector have almost nothing with health but have lot of money – so they will come to our lists too.
So far, Grief has dumped files in folders called “Accounting” and “Financial Agreements.”
The “Accounting” folder contained some files from 2015-2020 that dealt with routine business expenses, but also Profit & Loss statements for each year, and calculations of quarterly incentive compensation for named employees, up through Q1 of 2021. There were also figures related to a PPP loan and application for forgiveness of the loan.
From a security standpoint, and somewhat thankfully for them, it appears that bank account numbers were truncated, as were SSN of employees.
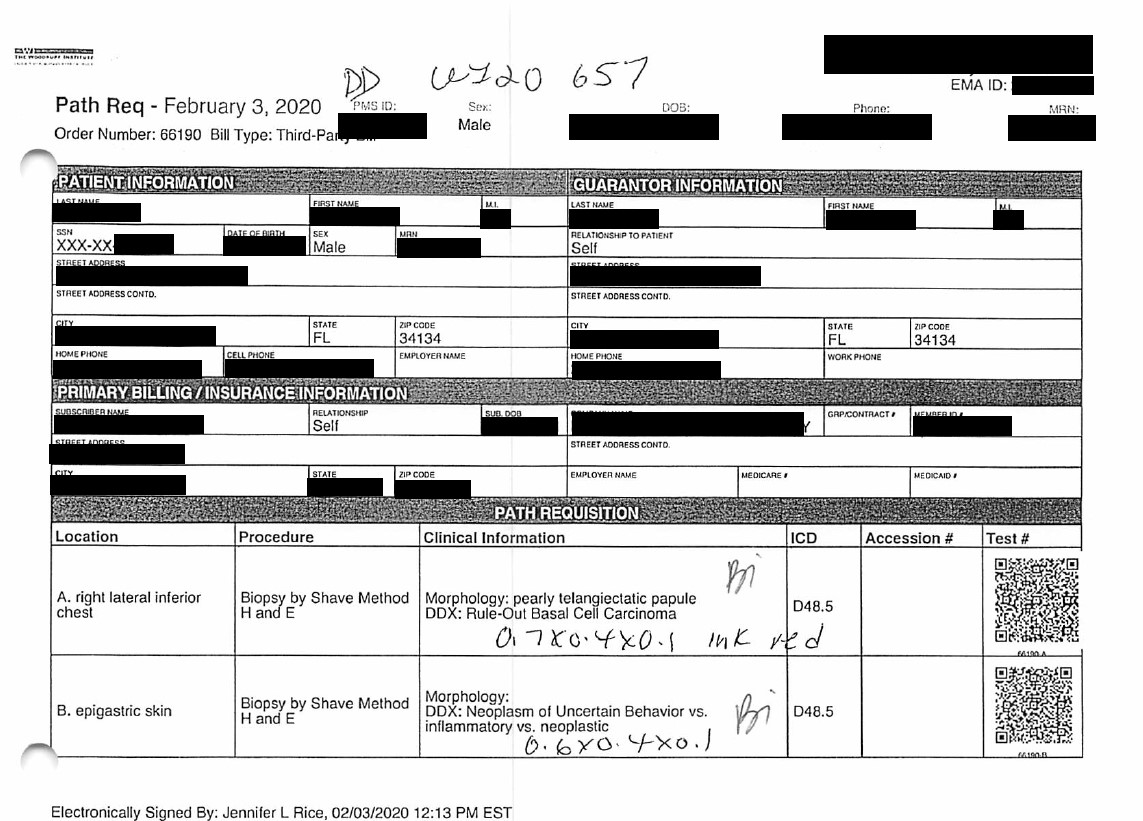
The “Financial Agreements” folder contained some files with patient protected health information. There were approximately 50 files from 2019 and 2020 relating to lab tests that revealed patients’ names, addresses, date of birth, telephone number (home and cell), health insurance information, type of test, and purpose. The only SSNs we spotted were in older files where Medicare numbers appeared to be the individual’s SSN.
There were also a few files from 2018 where patients had signed forms agreeing pay off fees by monthly credit card payments. In those cases, the full credit card number information appears on the form.
Grief has not indicated how much data they claim to have acquired from Woodruff, but what they dumped so far does not indicate any access to larger patient records databases.
DataBreaches.net sent email inquiries to Woodruff on June 12 and again on June 16 seeking more details, but they did not reply at all, despite having acknowledged receipt of the June 12 inquiries.
Additional material and editing by Dissent.