On Wednesday, Jukin Media posted a notice on its site requiring users to reset their passwords. They said the reset was due to a “security upgrade.”
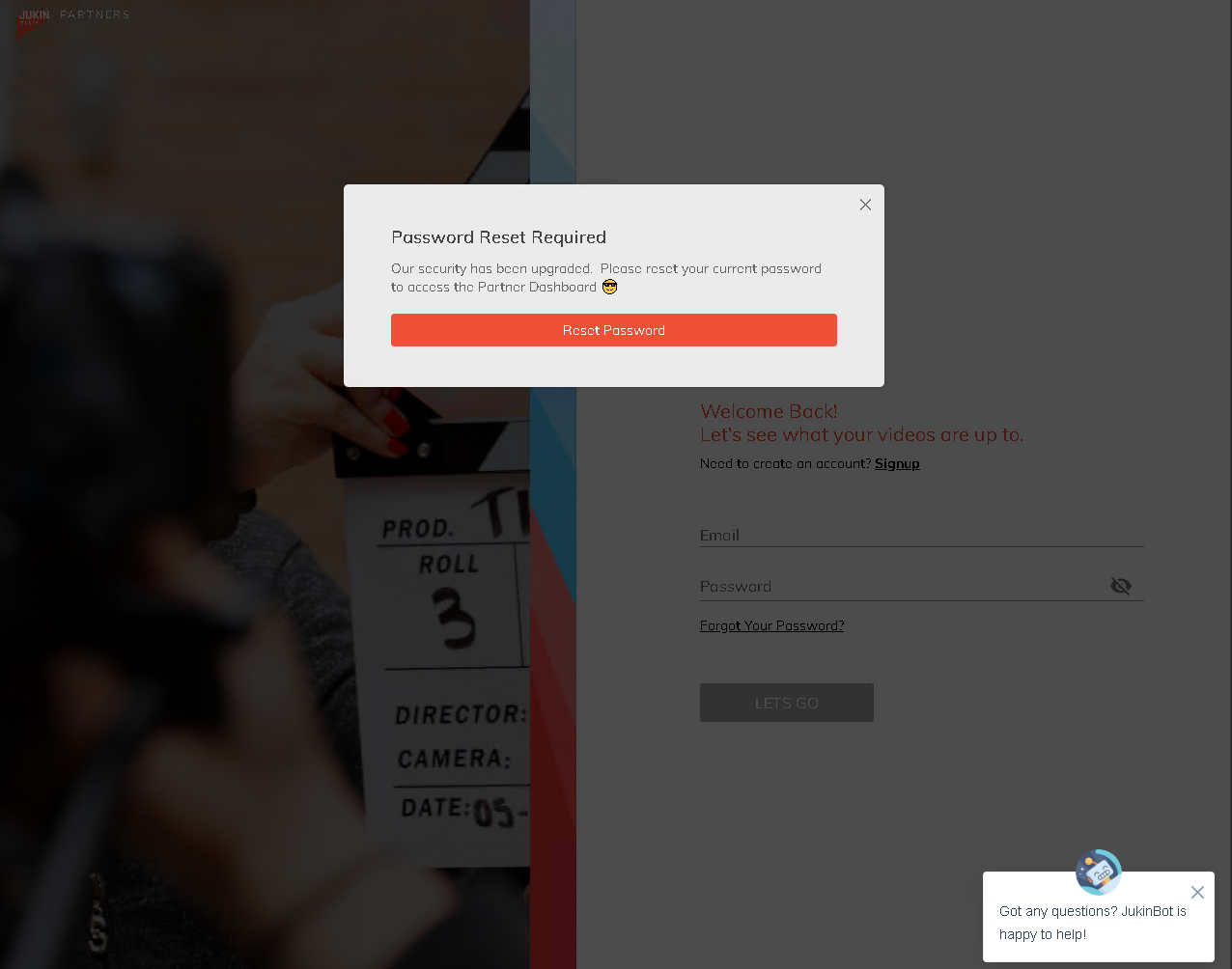
By now, whenever I see announcements about what seems to be an unplanned or unscheduled reset, I suspect a breach, so I reached out to Jukin Media’s Twitter team via DM to inquire.
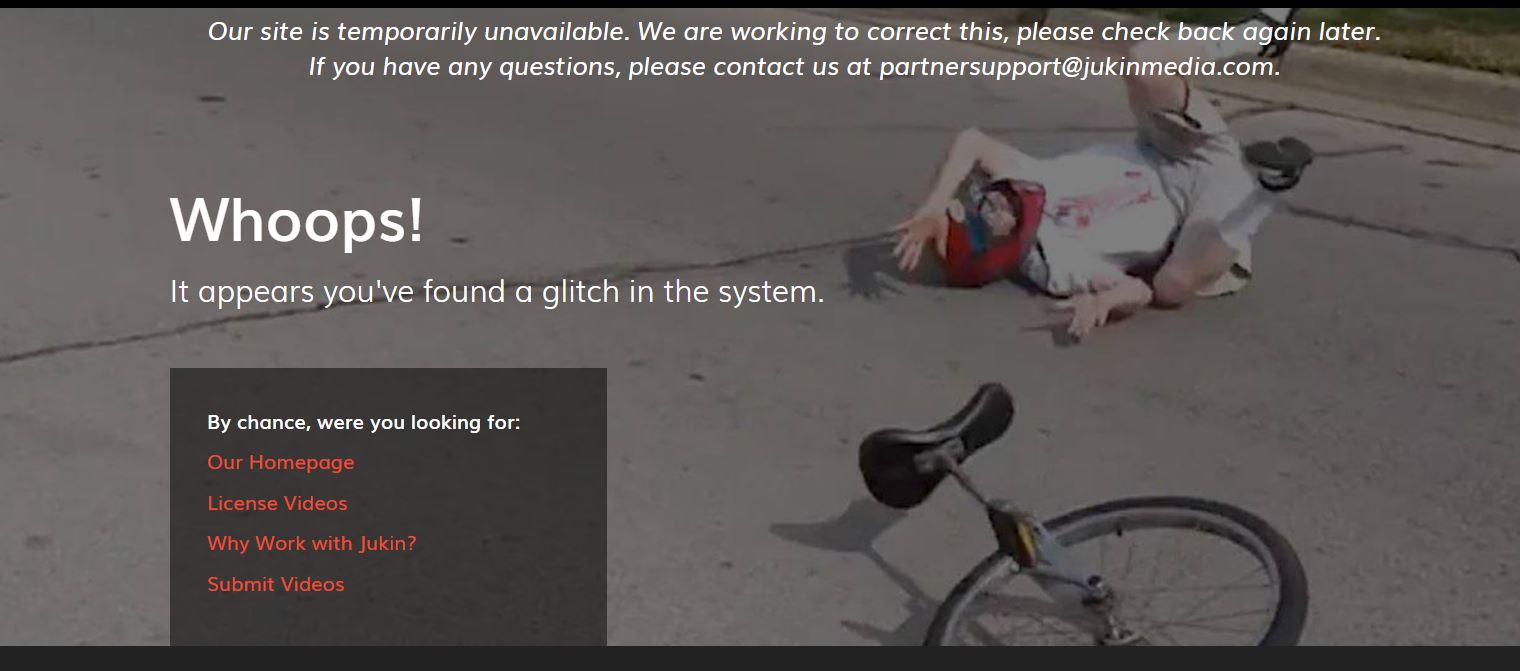
They did not respond, and over the next few hours, attempts to connect to their site failed with 504 messages. When I was finally able to connect to the site to send a press inquiry, clicking “submit” returned a “Whoops!” message that their site was temporarily unavailable.
Then later yesterday, it became clear that there had definitely been a security incident when a thread appeared on a popular forum dumping Jukin data for a nominal fee of 8 tokens.
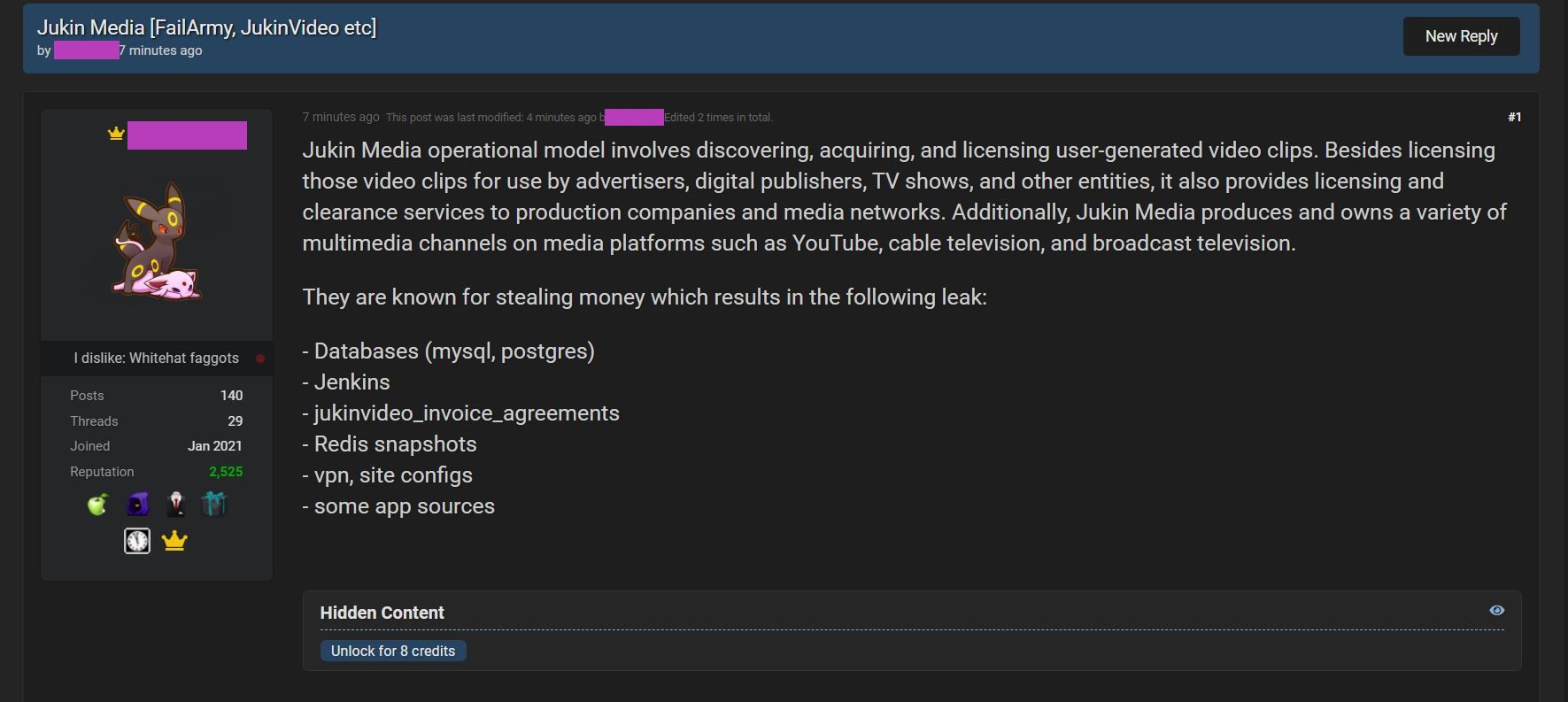
From the wording of the listing, someone was obviously angry at Jukin:
They are known for stealing money which results in the following leak:
– Databases (mysql, postgres)
– Jenkins
– jukinvideo_invoice_agreements
– Redis snapshots
– vpn, site configs
– some app sources
According to “Umbreon,” one of the individuals involved in the hack, “We had the popcorn ready and strapped in for a long ride.”
The ride might have been shorter had Jukin responded to the threat actors or followed up when they detected one of them. Jukin’s “Crescendo” reportedly detected and walled off ShinyHunters with a message: “stop please.”

But what did Jukin do then? It seems that they never detected — nor blocked — Umbreon at all. A lot of the data that was exfiltrated was reportedly exfiltrated after ShinyHunters was detected and blocked.

The fact that Jukin Media knew they were being attacked makes their “Security Upgrade” notice seem even more deceptive. Why didn’t they tell users that they knew they had been attacked and were requiring a password reset in response?
And why haven’t they said anything publicly since yesterday’s leak?
DataBreaches.net was able to submit a press inquiry today to Jukin Media through their web site, but no reply has been received as of the time of publication.