Lawrence Abrams reports:
The relatively new Bl00Dy Ransomware Gang has started to use a recently leaked LockBit ransomware builder in attacks against companies.
Last week, the LockBit 3.0 ransomware builder was leaked on Twitter after the LockBit operator had a falling out with his developer. This builder allows anyone to build a fully functional encryptor and decryptor that threat actors can use for attacks.
Read more at BleepingComputer.
Threats
While Bl00dy Gang develops its ransomware, it appears they are also testing its communications and pressure tactics. This week, they seem to have decided to use mafia tactics with death threats. On September 28, they wrote:
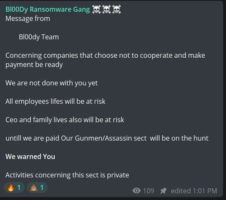
Concerning companies that choose not to cooperate and make payment be ready
We are not done with you yet
All employees lifes will be at risk
Ceo and family lives also will be at risk
untill we are paid Our Gunmen/Assassin sect will be on the hunt
We warned You
Activities concerning this sect is private