Gwyn D’Mello reports that an online music site was hacked to make a point after they failed to secure their site despite multiple warnings:
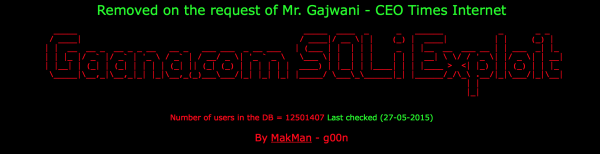
A white hat hacker used an exploit to gain access to Gaana.com user credentials, because they neglected to fix a security bug he reported.
It seems Gaana.com was hacked a few hours ago, with user data and credentials being accessed. But, in a fortunate turn of events, the responsible party turned out to be a white hat hacker.
[…]
Mak Man, the hacker responsible, detailed the incident in a Facebook post, saying he had reported the exploit to the website’s team on multiple occasions, but was ignored. He says he was trying to bring attention to the glaring hole in their security, and had no malicious intent.
While users’ credentials were accessed, Mak Man has since said that the data was being queried in real time, and was not stored or copied on their server.
Read more on DNA.
The site notes that all its passwords were hashed. See their tweets about the incident.
I don’t understand the logic here. All the so-called white hacker had to do is expose the vulnerabilities to a major news source. I have seen too many cases where even if it is the hack was made with good intentions, the person is treated like a criminal for going too far. Even though data was not supposedly stored on their servers and was queried in real time, it doesn’t mean the data can’t be copied out.
His no malicious intent theory is flawed – he breached a website and creates bad news… Thats ok ? He obviously doesn’t think in the corporate mindset. Should the corporation decide to go after him, he will probably be hard pressed to find a good legal stance on what he has performed.
I think going to the media would be preferable to what he did, but I do understand the frustration of trying to warn/alert sites numerous times only to have them not do anything.