The blackhat using the Twitter handle @tdohack3r (TheDarkOverlord) has put yet another database with patient information up for sale. As with previous hacks, the database contains identity information that could be used for identity theft or fraud. It also contains medical insurance account information and codes related to the type of service.
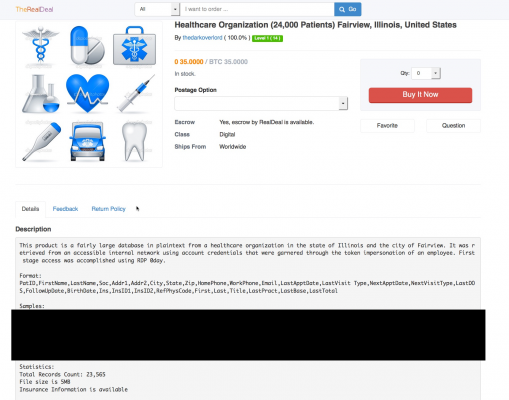
According to the listing on TheRealDeal Market, the database consists of 23,565 patients’ records. TheDarkOverlord has not yet indicated publicly whether the entity, who is not named in the listing, has been or will be sent a ransom demand, although that has been the hackers’ M.O. so far, it seems.
The database was allegedly “retrieved from an accessible internal network using account credentials that were garnered through the token impersonation of an employee.” As with some other attacks, the hacker(s) claim to have used a RDP 0day that they discovered.
The patient records are in the format:
PatID,FirstName,LastName,Soc,Addr1,Addr2,City,State,Zip,HomePhone,
WorkPhone,Email,LastApptDate,LastVisitType,NextApptDate,NextVisitType,
LastDOS,FollowUpDate,BirthDate,Ins,InsID1,InsID2,RefPhysCode,First,
Last,Title,LastPract,LastBase,LastTotal
From medical codes in the sample data and from a July 1st tweet from TheDarkOverlord with images, DataBreaches.net identified the likely affected organization. Their facility is closed over the weekend, however, so DataBreaches.net has left them an inquiry. DataBreaches.net has also attempted to contact some of the patients, but has received no response as yet. This will be updated as more information becomes available.
Update 1: Well, someone at the entity who answered the phone yesterday first seemed to acknowledge that they were hacked, and transferred my call to someone else, who claimed she had no idea what I was talking about. So I called back and started again, and ran into “We have no idea what you’re talking about responses.” Interesting. Either they are in coverup mode or a lot of the employees are clueless.
In any event, it is P&O Care that is the hacked entity. I do hope they issue a statement, although they have ignored a few messages from me. As of yesterday, some of their patients’ data had been dumped on a public paste site, and then there were those pictures…