Cassidy Williams reports:
Hundreds of dental offices across the country were targeted in a ransomware attack. PerCSoft, IT company that was attacked, is based out of West Allis. It wasn’t immediately clear whether patient data, including Social Security numbers, was compromised.
Read more on Fox6.
As Catalin Cimpanu reported on ZDNet, PerCSoft collaborated with The Digital Dental Record to produce DDS Safe, a medical records retention and backup solution. Ironically, their home page might suggest that their product will keep you from becoming a ransomware victim.

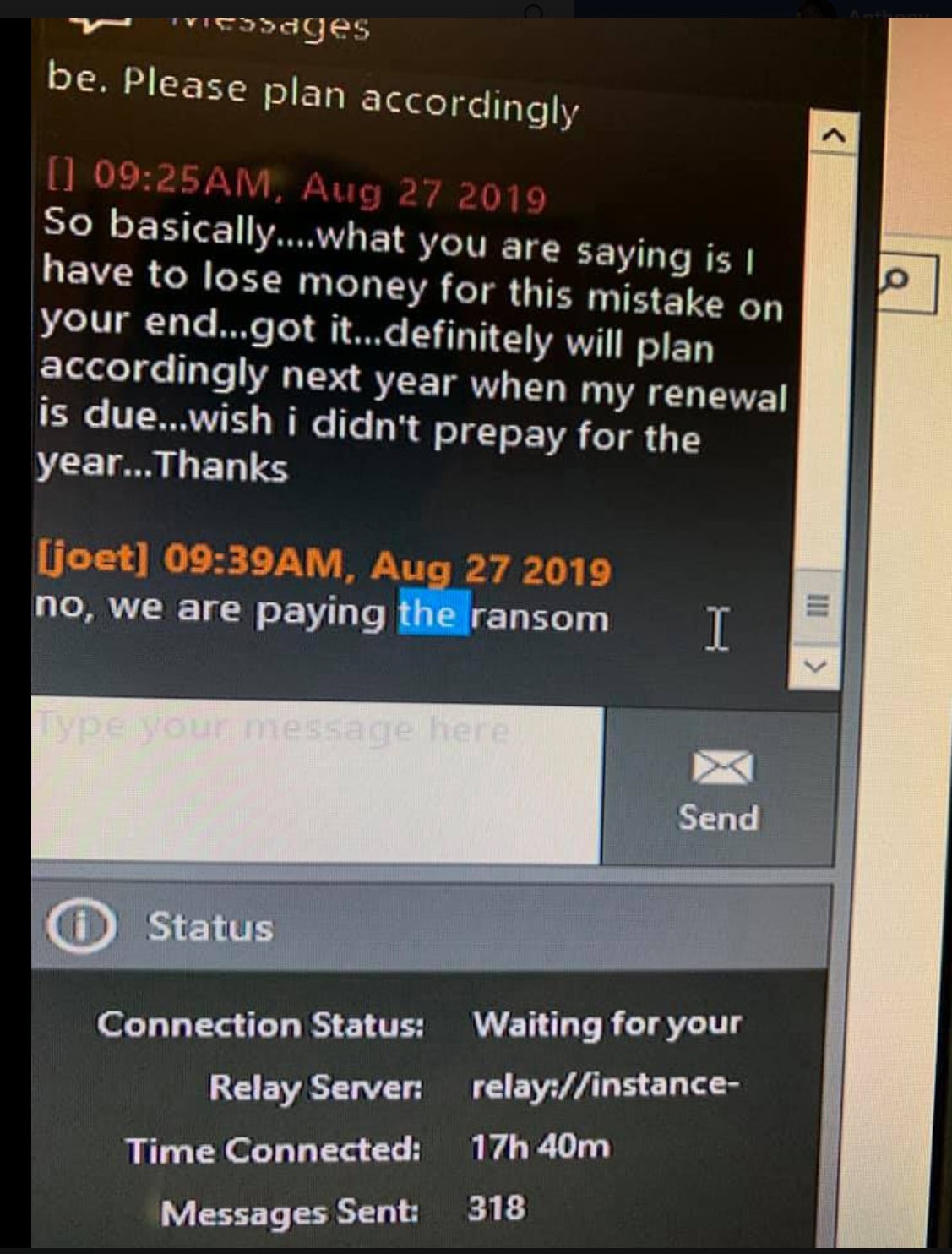
But as Cimpanu reports, and as indicated by a screencap that has been circulated on the internet stating that the company was paying the ransom demanded:
Over the last weekend, a hacker group breached the infrastructure behind this software, and used it to deploy the REvil (Sodinokibi) ransomware on computers at hundreds of dentist offices across the US.
The security breach came to light on Monday, when dentists returned to work, only to find out they couldn’t access any patient information.
A source impacted by the ransomware tells ZDNet that the two companies opted to pay the ransom demand.
A source sent the following screencap to DataBreaches.net. It allegedly is from a chat between one of DDS’s clients and “JoeT:”