As posted by @bitsdigits on Twitter tonight:
Just when you think the US Federal and Intelligence agencies were done being breached. This happens. DISA, the Defense Information Systems Administration has suffered a compromise of epic proportions. But here’s a notification for your troubles.
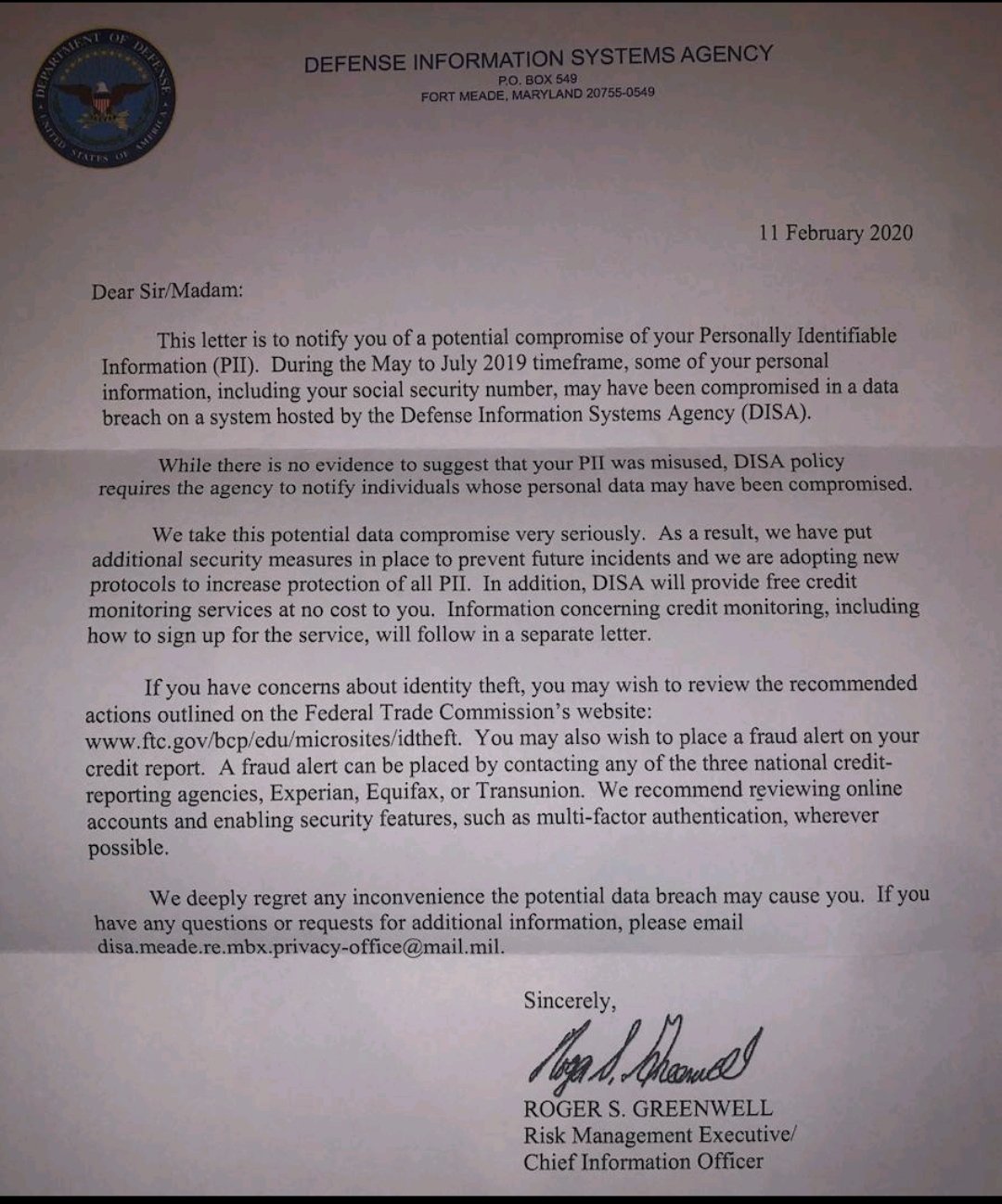
The notification, dated February 11 and signed by Roger S. Greenwell, Risk Management Executive, Chief Information Officer, explains that the recipient’s personally identifiable information may have been compromised between May to July 2019. The letter does not explain why it took until February of 2020 to make the notifications.