Apex America describes itself as a leading Digital Customer Experience services company in Latin America that partners with more than 50 global brands. It has operational centers in 14 locations in Latin America.
That’s how they describes themselves. The threat actors known as REvil (Sodinokibi) describe them as targets who have so far refused to pay ransom demands.

As is its usual procedure, REvil added a listing for the firm to their dedicated leak site. This time, they only posted a few screencaps as proof of claim, noting:
At the moment, we are conducting a full analysis of all the documents we have, this is a small part of the total amount of data.
Some of them will be published, others will be sold. We are ready to listen to offers from buyers in a private chat.
So far, Apex America does not seem to have posted any notice on their site. DataBreaches.net reached out to their social media team to ask them if they could confirm the breach or offer any statement (the web site directs people to use social medial for such contacts, it seems). They have not responded, even though they have been online since the request was sent through DM.
DataBreaches.net was able to see some of REvil’s attempts to persuade Apex America to pay what was originally set as a $7 million ransom. After a number of days, someone presumably from Apex America (although that has not been confirmed) showed up in the chat to ask REvil what their lowest price would be. REvil answered “6kk” ($6 million). That was 5 days ago, and Apex America or whoever it was in that chat has not responded since.
One day ago, REvil’s negotiator posted, “Your silence makes everyone nervous. We repeat, we are doing business, not war.”
There was no response, and REvil has since posted the listing on their leak site and raised the price:

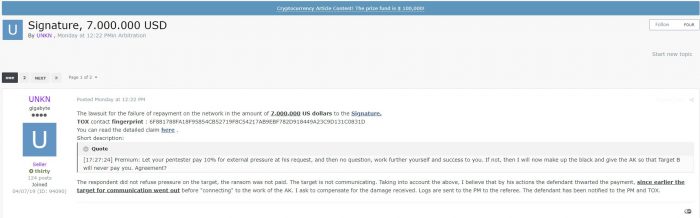
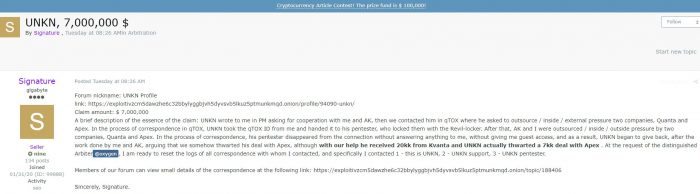
Additional drama involving the threat actors has also surrounded the Apex America incident, with “UNKN” of REvil and “Signature” each suing each other for $7 million through the arbitration forum on a popular Russian-language forum. To the dismay of some forum members, REvil and Signature hung some of their dirty laundry out in public, each basically blaming the other for the loss of $7 million ransom in the Apex America operation. “Signature” claims that UNKN reached out to him to recruit him for work on Quanta and Apex America, but then REvil did not follow through on their deal.
Their dispute is interesting to read for the insights it provides into their operations and communications, but neither party got any joy from the arbitrator/moderator, “@oxygen,” who denied both of their claims, noting that in the arbitration rules, claims for loss of profits are not accepted.
Based on the situation, it is clear that the parties worked on partnership terms and each received his share of the profit.
In case of failure, both sides get nothing.
The topic is closed.
The topic may be closed for UNKN and Signature, but there’s still the matter of REvil allegedly having some as yet unspecified amount of Apex America’s files.
This post may be updated as more details become available.
Reporting by Chum1ng0 with some additional material and editing by Dissent.