Here we go again — another ransomware attack on a k-12 school district, and the threat actors may have obtained current — and very old — data on both students and personnel. Kudos to the district for promptly alerting their community as to the possibility and risks, but still, this is serious. So far, this incident has not shown up on any leak site on the dark web, but it is quite possible or likely that we will see a data dump at some point, assuming the district holds firm and does not pay any ransom demands.
Valerie Myers reports:
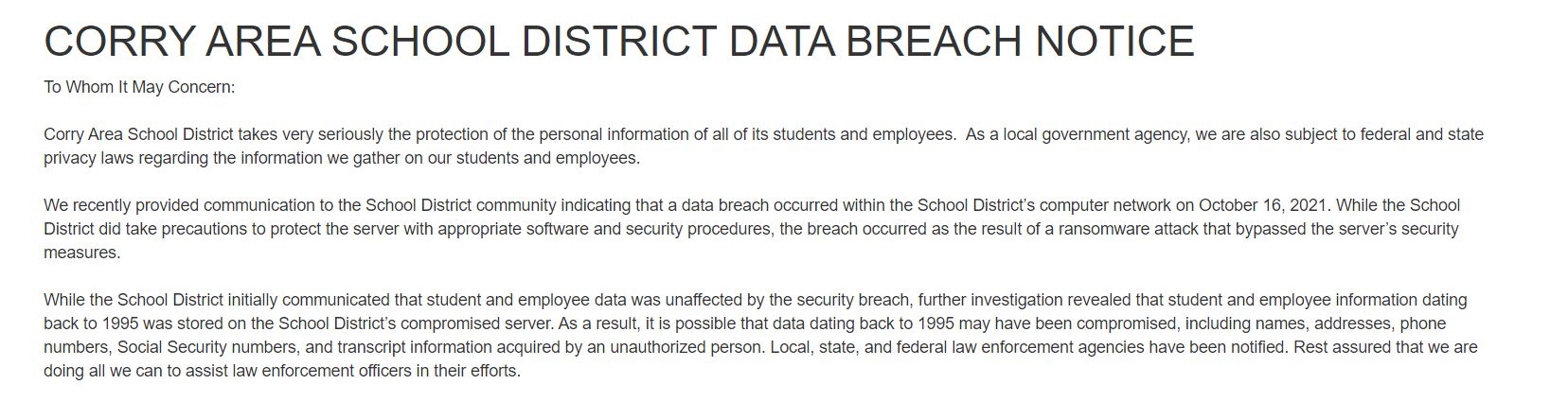
Personal information on Corry Area School District students and staff might have been exposed in a ransomware attack on the district’s computer network on Oct. 16.
Student and staff names, addresses, phone numbers, Social Security numbers and transcript information dating back to 1995 could have been obtained by the cyber attacker, district officials said in a post on the district website at corrysd.net.
Read more on Erie Times-News.