Br: National Fund for Educational Development (FNDE) hit by ransomware
On September 3, the RansomExx group leaked 62 TB of files from the National Fund for Educational Development (FNDE). FDNE is a federal agency of the Ministry of Education, and is responsible for implementing programs such as the National School Nutrition Program.
FNDE provided a statement to CISO Advisor, stating that as soon as they became aware of a possible leak, the Directorate of Technology and Innovation acted promptly. There was no compromise of the municipal services, and the only data that was leaked was already public.
Pt: Ourique Municipality targeted by ransomware attack
The municipality of Ourique announced a cyberattack on their Facebook page on Wednesday. No one has as yet claimed responsibility for the attack and there has been no mention of any ransom or any negotiations.
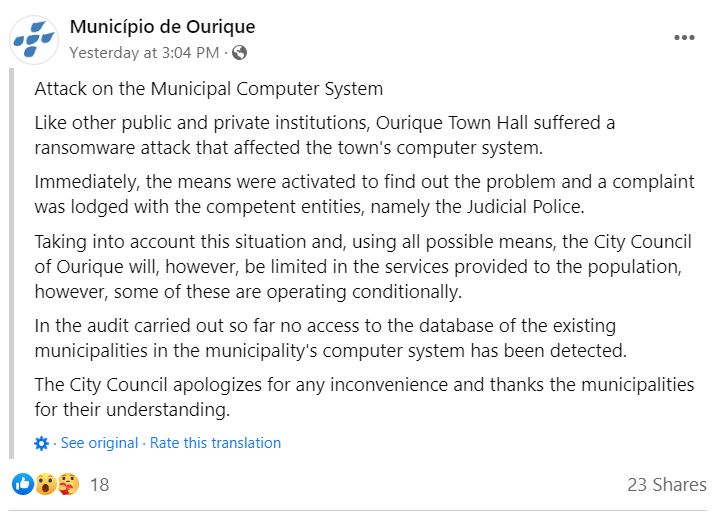
Attack on the Municipal Computer System
Like other public and private institutions, Ourique Town Hall suffered a ransomware attack that affected the town’s computer system.Immediately, the means were activated to find out the problem and a complaint was lodged with the competent entities, namely the Judicial Police.Taking into account this situation and, using all possible means, the City Council of Ourique will, however, be limited in the services provided to the population, however, some of these are operating conditionally.In the audit carried out so far no access to the database of the existing municipalities in the municipality’s computer system has been detected.
The City Council apologizes for any inconvenience and thanks the municipalities for their understanding.
Cl: COVID-19 tracking platform of a mining company compromised
Attackers compromised the DB of COVID-19 tracking platform of the Codelco mining company and have listed it for sale on a popular forum. There are almost 17,500 emails and more than 1,800 are from corporate users. Some of the fields include, name, address, phone number, email address, vaccination, and date of birth.
Tweet:
Atacantes comprometieron DB de plataforma de seguimiento de COVID-19 de importante compañía minera ?? hay casi 17.500 correos y más de 1.800 son de usuarios corporativos. #AlertaPhishing
Algunos campos de “t_personal”: rut, email, telefono, nacimiento y vacunas entre otros ? pic.twitter.com/y4BqxFd4Kl
— Germán Fernández (@1ZRR4H) September 8, 2022
Pe: Lacalera victim of ransomware attack
“La Calera Agricola is a leading company in the production and export of citrus fruits in Peru,” writes LockBit 3.0 in adding LaCalera to their leak site. But then LockBit linked instead to lacalera.pe, which is the same family, but a different part of their business focused on egg production and marketing. Did LockBit compromise both divisions of the business or just one, and if just one, which one? DataBreaches has sent an inquiry to LaCalera seeking clarification, but received no reply by publication.
LockBit has not leaked any data or proof as of the time of this publication.
Editing and additional reporting by Dissent