Belgium: CHU St. Pierre Cyberattack
DHnet in Belgium reports that Saint-Pierre hospital in central Brussels temporarily closed its emergency room and diverted line 112 to other institutions due to a cyberattack early Saturday morning. The attack reportedly disrupted the functioning of many applications, including patient records and telephone lines.
By 5:00 pm Brussels time, most of the blocked apps were functional again. Line 112 and emergencies are expected to be restored later in the evening.
CHU Saint-Pierre is a local public university hospital consisting of two sites, 40 medical services, and 19 themed clinics. They perform 19,000 surgeries per year and 400,000 consultations.
There has been no statement indicating who the attackers might be and whether there has been any ransom demand.
Brazil: Grupo Hospitalar Vida’s hit by LockBit
The hospital system’s website is unreachable at publication time.

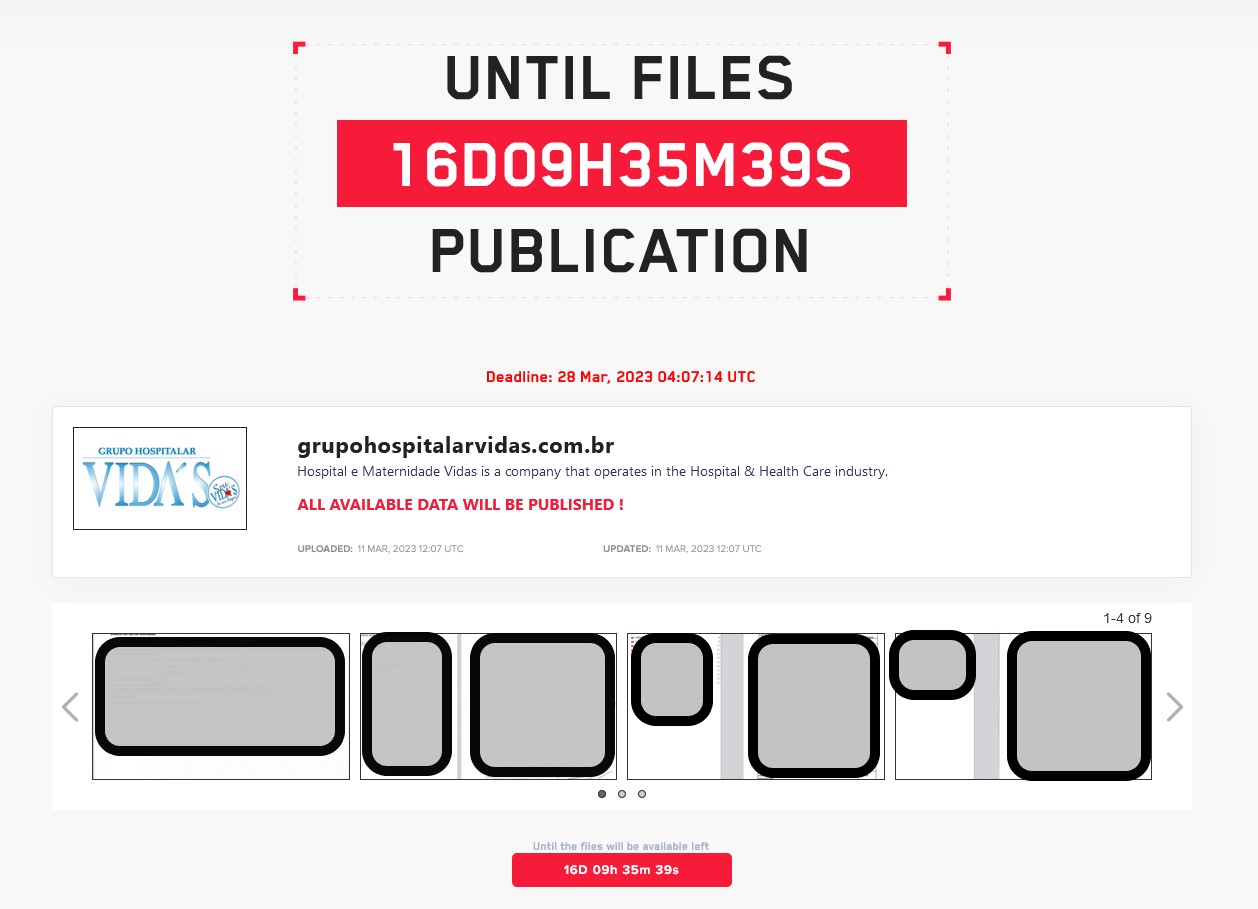
LockBit has consistently failed to live up to its stated policy about not attacking hospitals. After a recent incident involving Sick Kids Hospital in Canada, LockBit apologized and provided them with a decryption key, claiming that an affiliate had violated policy and been terminated. Pretty much no one believed that.
Now a hospital system with a maternity hospital has been hit. What will LockBit do now?
France: CHU Brest-Carhaix cyberattack
Le Télégramme reports that the university hospital center (CHU) of Brest-Carhaix was the subject of a cyberattack on Thursday evening.
According to a statement from the hospital on Friday, “We were warned by the National Information Systems Security Agency (Anssi) of a cyberattack that affected hospital servers on Thursday evening. It may have been blocked before it was completed, so there was no ransom demand or health data leak. At this stage, we do not have the elements for analyzing the operating mode, nor have we detected any flaws in our security system.”
As of yesterday, the hospital was operating in degraded mode without any internet connection. All information systems in Brest and Carhaix were cut off, as were interactions with the outside world.