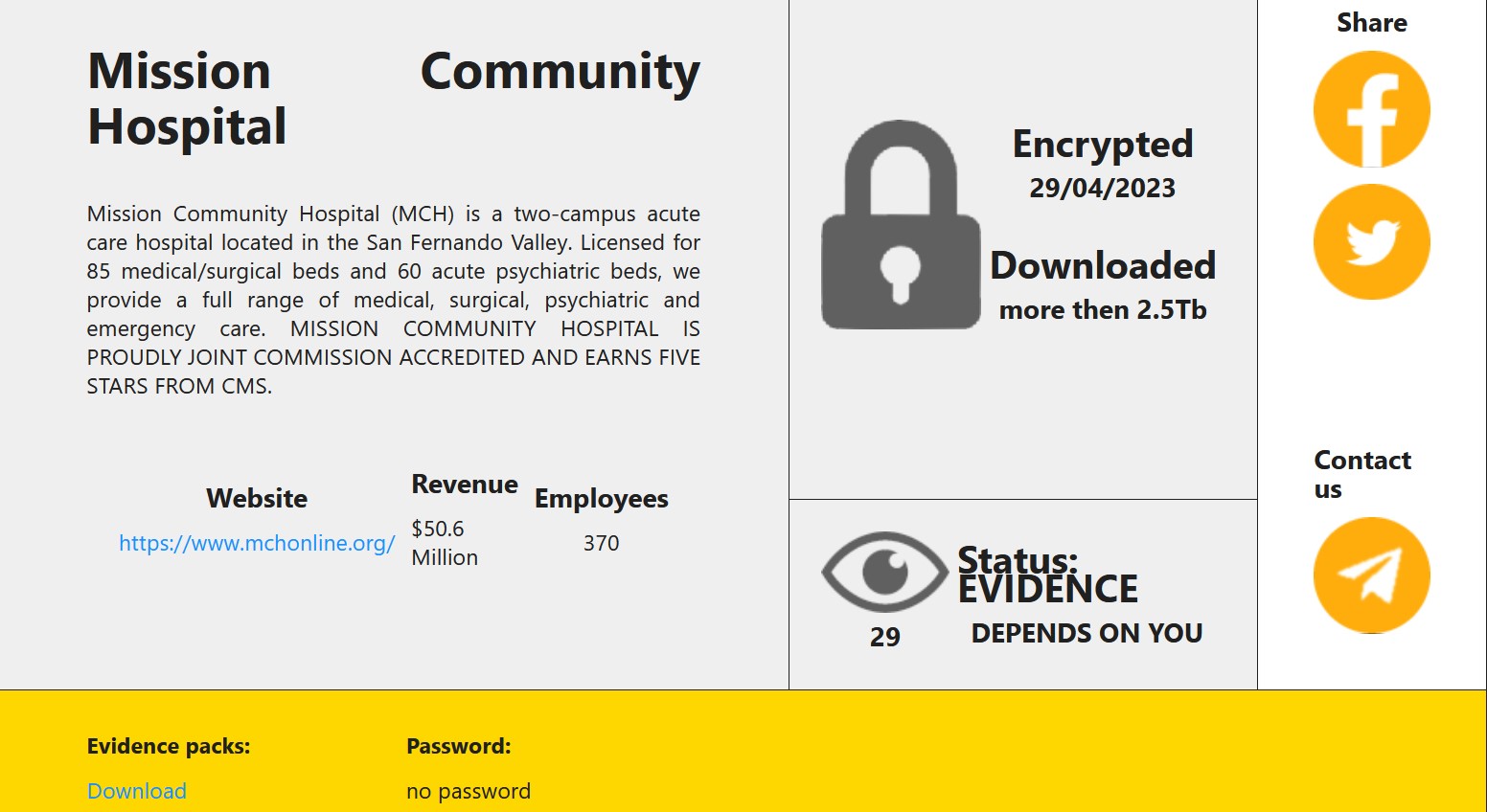
Mission Community Hospital in California allegedly experienced a ransomware attack on April 29.
On Wednesday, RansomHouse threat actors claimed responsibility for the attack and provided a number of files as proof. They claim to have downloaded 2.5 TB of data.
From the proof files, it appears that RansomHouse accessed the imaging system and image files as well as employee-related files and some financial reports and files. The only patient references in the proof files were older files in backups. Whether they obtained any current patient information or the EMR system remains to be seen. DataBreaches has reached out to RansomHouse on their Telegram channel but they have not been responsive in the past, so they may not answer this time, either.
There is no statement or notice about any incident or breach on the hospital’s website. DataBreaches has sent an inquiry asking them about the claimed attack and their response to date. This post will be updated if a reply is received or more information becomes available.