Pulmonary Physicians of South Florida (PPSF) describe themselves as a group of experienced and highly qualified pulmonary, critical care and sleep medicine physicians. “We provide comprehensive, state of the art diagnosis and treatment of diseases of the lungs in every hospital in Miami-Dade County, as well as in select hospitals in Broward and Monroe counties,” they claim, suggesting that they have a large practice and may have a great deal of protected health information on their system.
On February 19, the ransomware group known as Brain Cipher added the provider to their dark web leak site with proof of claims. The proof consisted of screenshots of a medication request for a named patient and a partial listing of folders on a drive, where the folder names appeared to be patient last name and first name with the patient’s date of birth as part of the folder name (e.g., lname fname MM-DD-YYYY). The screenshot also displayed folder names for internal files.
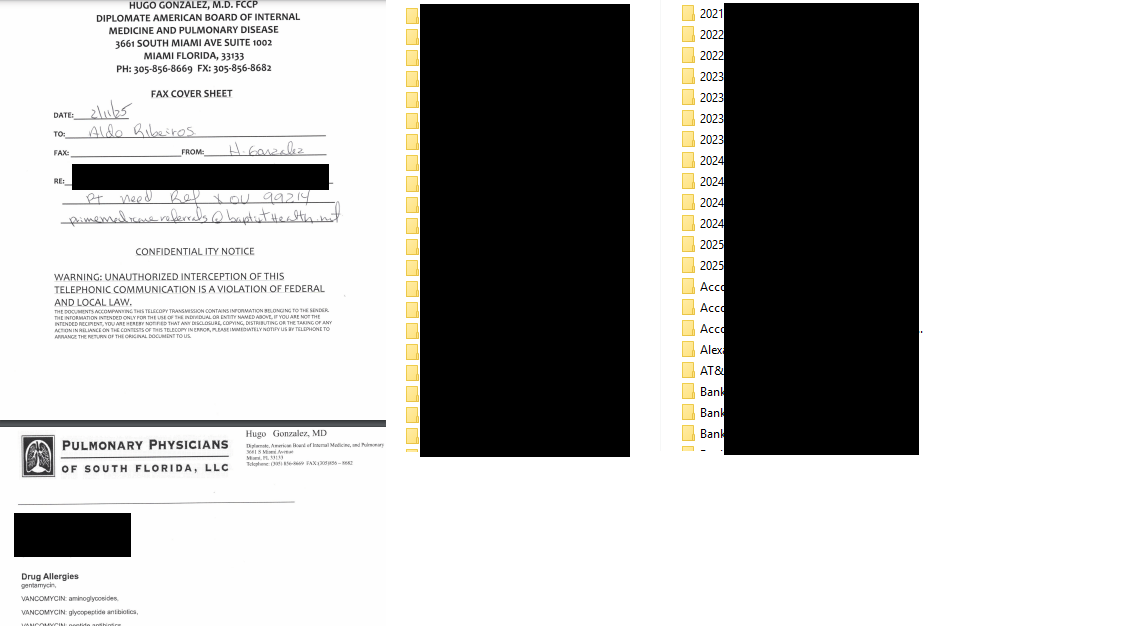
Brain Cipher’s listing does not indicate when they first attacked PPSF or how many files or GB or TB of data were acquired, but the other part of their proof of claims consisted of a file tree that lists 423,920 files. The file names generally consist of the patient’s name with a date of service, and some indication of the contents of the file or record (e.g., whether it was a scan or a progress note, etc.). Because there were often multiple files for each named patient, the 423, 920 does not represent the number of unique patients but may possibly represent the number of records acquired by the threat actors. Some of the files appear to be related to depositions in litigation.
Finding no notice on the physicians’ web site or any press release, DataBreaches reached out to the provider last week via their on-site contact form and again today, with questions about the alleged attack and their response. DataBreaches also emailed Brain Cipher to request some additional details. Neither the provider nor the threat actors have replied as of publication.
At this point, then, we have no confirmation from PPSF, and Brain Cipher did not reveal when the alleged attack occurred. Did it happen shortly before their leak site notice or did it occur months ago? How many patients were affected? Did Brain Cipher lock any of their files or systems? Was patient care affected at all?
There is much we do not yet know — including whether PPSF will confirm or deny that they experienced any breach. This post will be updated if more information becomes available.