The Technion, which is the Technology Institute of Israel, confirms it has been the victim of a ransomware attack by threat actors demanding 80 BTC ransom to unlock the data.
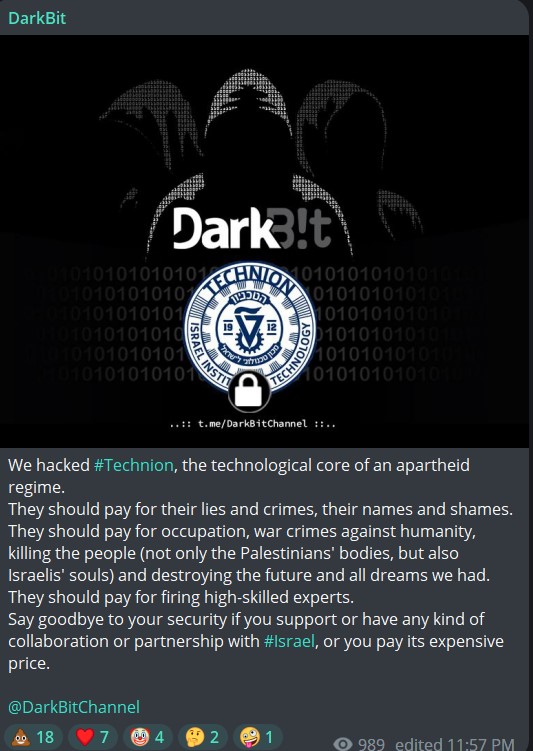
According to the ransom note sent by attackers, the school’s network was locked. Their ransom note, first published by Erez Dasa on Telegram, begins:
Dear Colleagues,
We’re sorry to inform you that we’ve had to hack Technion network completely and transfer *all* data to our secure servers.
So, keep calm, take a breath and think about an apartheid regime that causes troubles here and there.
They should pay for their lies and crimes, their names and shames. They should pay for occupation, war crimes against humanity, killing the people (not only Palestinians’ bodies, but also Israelis’ souls) and destroying the future and all dreams we had.
They should pay for firing high-skilled experts.”
The note, which also warns Technion not to try to decrypt files without the key, gives Technion 48 hours to pay 80 BT ($1.74 million) before the price goes up 30%. After 5 days, the data will be put up for sale, the attackers, who sign the note “DarkBit,” threaten.

A spokesperson for the institution confirmed the attack to Ynet, who reports that despite the cyber attack, exams at the Technion are taking place today as usual. However, the students were asked to disconnect their personal computers from the network and reduce email traffic until further notice. In email to DataBreaches, however, Dasa reports that all exams have since been canceled for the 13th and 14th.
Attempts to contact DarkBit via the TOX ID in the ransom note failed and returned an invalid ID message.

Comment
And what is DarkBit’s real motivation? Rather than the usual “It’s just business” type of note, DarkBit’s note suggests that they are trying to sound almost like hacktivists, but their explanation sounds more like former employees of Technion who were fired or who blame Technion for their professional failures. How did Technion “destroy the future and all dreams” they had? What “high-skilled experts” did Technion fire — was it them? Is that why they addressed the note to “Dear Colleagues?”
Later in their ransom note, they add a common warning to victims not to try to decrypt locked data without a key. But then these attackers add, “”You have to trust us. This is our business (after firing from high-tech companies) and reputation is all we have.”
So they are claiming they were fired from high-tech companies? If they were fired from high-tech firms, that doesn’t exactly support a claim of “reputation is all we have.” DarkBit is an unknown group with no publicly known history or reputation of keeping their word to provide a key if victims paid.
But then, all of their explanations may be just fiction or cover up for some state-sponsored action, as Erez Dasa suspects.
This post will be updated if more information becomes available.
Update: It seems DarkBit has a Telegram channel and other social media accounts.