LockBit’s old leak site — the one seized by a coalition of law enforcement agencies under Operation Cronos — has been resurrected.
As it did in February when LockBit victim listings were replaced by teasers about what information law enforcement would be releasing, the old leak site reappeared on Sunday with new teasers about what law enforcement will be disclosing tomorrow. But will they have any new developments as exciting as when they announced in February they had seized 34 servers, frozen more than 200 crypto accounts, made some arrests, and had a free decryptor available to LockBit victims?
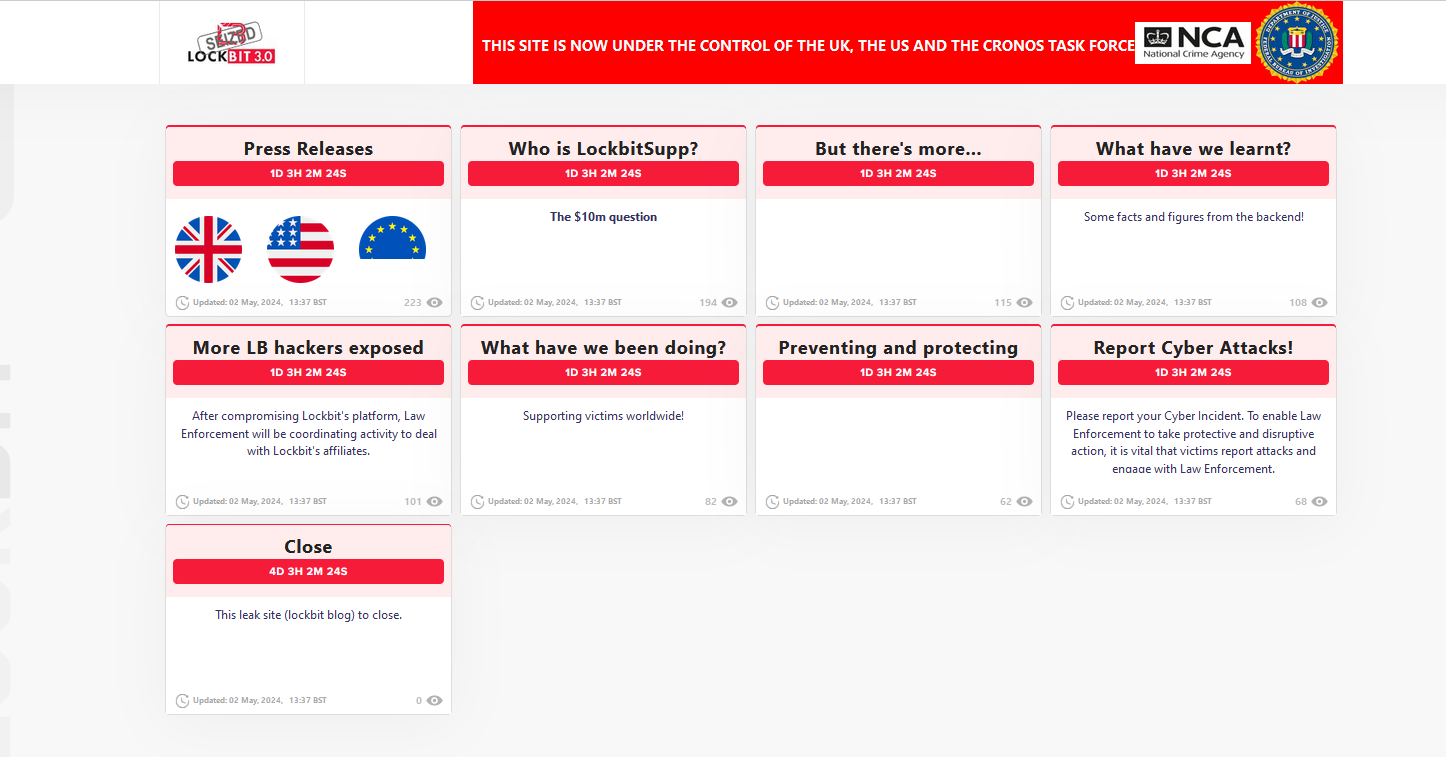
The teasers promise to expose more LockBit hackers, but once again, most eyes are probably focused on the “Who is LockBitSupp?” Will law enforcement actually reveal his identity or an arrest? That didn’t happen in February when they also posed the question, and if anyone thinks that LockBitSupp might be in custody, DataBreaches’ sources who have communicated with him over the past two days tell us that he is alive and is not in custody. What he is doing publicly seems to be re-posting a lot of old listings. What he might be doing behind the scenes is yet to be revealed.
Perhaps law enforcement will reveal his identity or more about it, but it seems they are unlikely to announce his arrest. Last time, they told us he wasn’t in the U.S, but had anyone really believed he was? For some reason that DataBreaches can no longer remember, we thought LockBitSupp was in Kazakhstan. We’ll see what law enforcement tells us tomorrow.
Unlike in February, where releases were published over days, all of the new releases from law enforcement are scheduled to be published simultaneously on Tuesday morning at 14:00:00 UTC (10:00 am Eastern). Stay tuned.
Update: They did name and indict someone they claim is LockBitSupp.