Graham Cluley sets the stage nicely:
Ouch.
One week after the French branch of cyberinsurance giant AXA said that it would no longer be writing policies to cover ransomware payments, the company’s operations in Thailand, Malaysia, Hong Kong, and the Phillippines have reportedly been hit… by a ransomware attack.
Read more on GrahamCluley.com.
Consistent with their typical method, the Avaddon threat actors added Axa to their dedicated leak site, posted a deadline, and a warning as to what would happen if Axa does not pay.
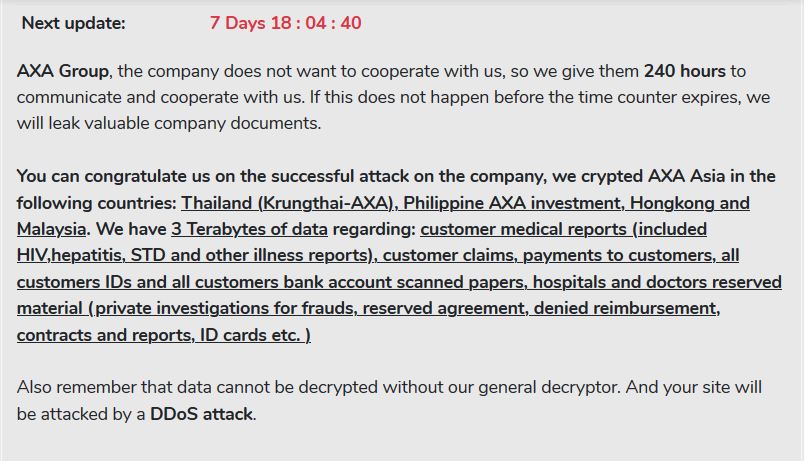
You can congratulate us on the successful attack on the company, we crypted AXA Asia in the following countries: Thailand (Krungthai-AXA), Philippine AXA investment, Hongkong and Malaysia. We have 3 Terabytes of data regarding: customer medical reports (included HIV,hepatitis, STD and other illness reports), customer claims, payments to customers, all customers IDs and all customers bank account scanned papers, hospitals and doctors reserved material (private investigations for frauds, reserved agreement, denied reimbursement, contracts and reports, ID cards etc. )
Also remember that data cannot be decrypted without our general decryptor. And your site will be attacked by a DDoS attack.
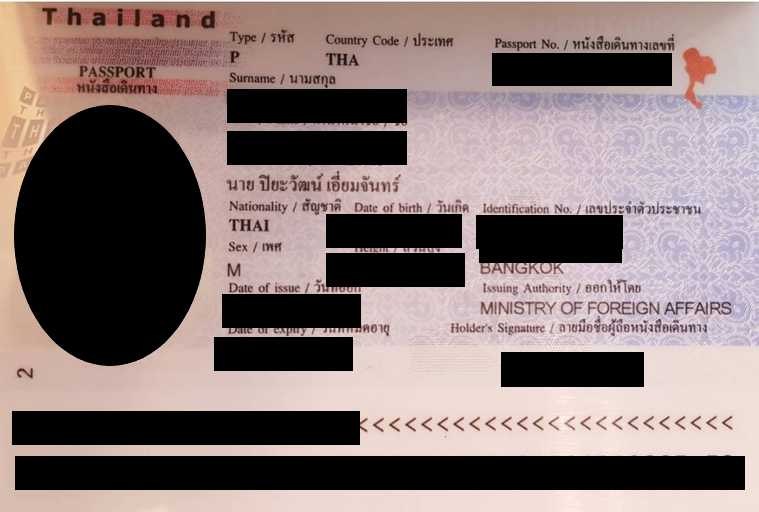
As proof of claim, they uploaded a number of documents allegedly taken from Axa. The documents included personal identification documents, such as the passport image redacted by DataBreaches.net, below, as well as corporate documents.
The threat actors have given the firm another week to respond.
So what will Axa do? As Cluley noted, Axa recently declared that they will no longer write new policies in France that cover ransom payments, although existing policies would not be affected, and they would continue to write policies that include recovery costs from ransomware attacks. Will they now decide to pay ransom themselves?
If their listing disappears from Avaddon’s leak site, that may indicate that they have paid or are negotiating. But if the listing remains, I guess we’ll see what happens in a week from now.