Groove, who is making a point of telling anyone who will read their site that Groove is not a gang but just a single person out to prove how easy it is to manipulate media, joined the ranks of those who attack medical entities without regard for the harm they may cause. It appears that Groove has attacked TriValley Primary Care in Pennsylvania, a medical practice with eight locations.
In a warning on Groove’s site, the threat actor cautions TriValley to return to the chat (to presumably resume negotiations). The following is a machine translations of the original Russian:
Think about your patients first.
Tomorrow I will not see an adequate offer in the chat, we will start flooding your office and add to the site, then I will go even further.
250k is mere pennies, I don’t need to whine in the chat, what a bad life, I had to think before
This morning, TriValley’s site was unreachable with a message that its resource limit had been reached.

When the site could be reached, the following notice was prominently placed on its home page:
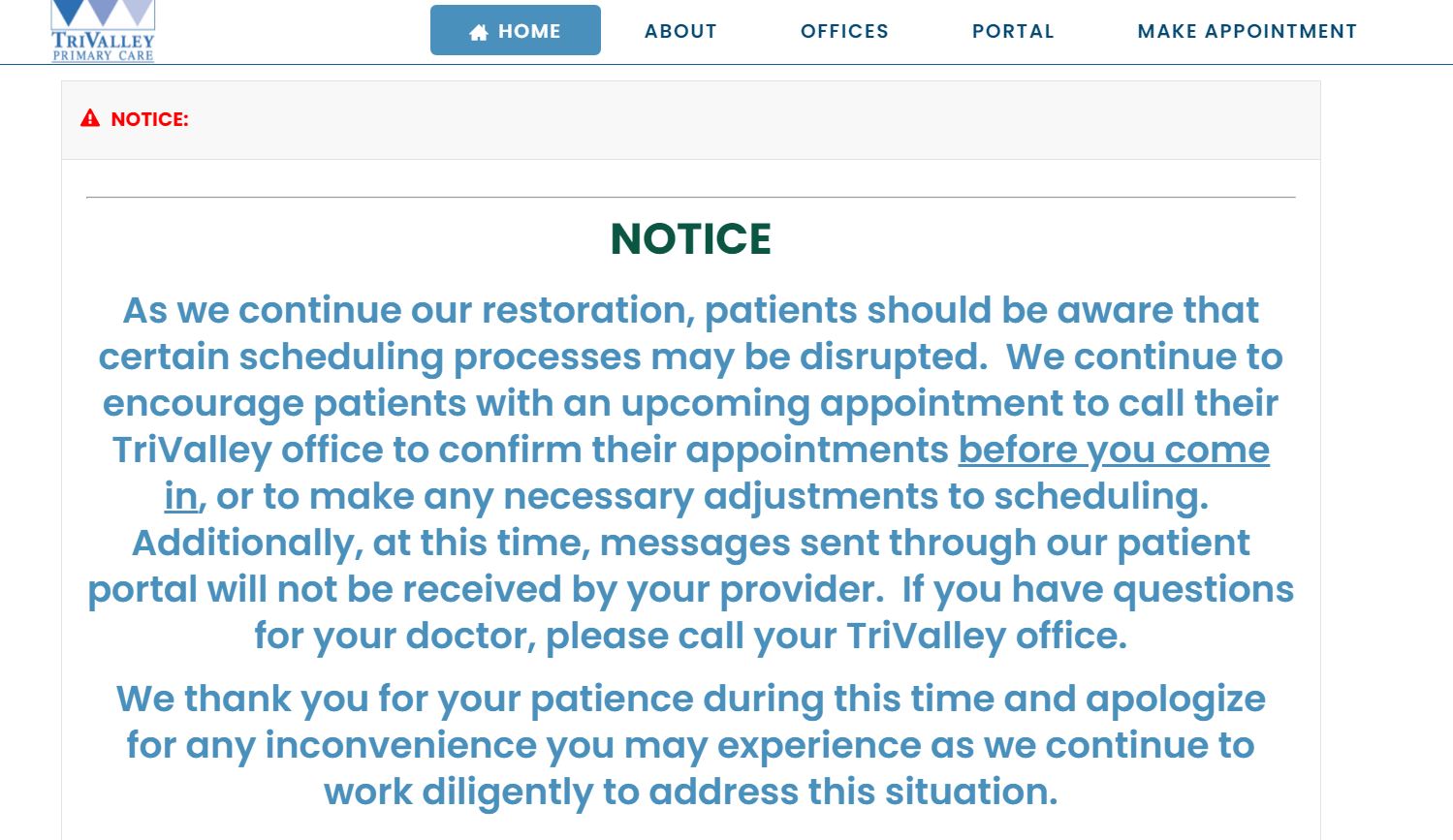
So while they have not actually confirmed that they were attacked by Groove, the status of their web site offers some confirmation of the claimed attack.