If Herman’s Hermits sang about the latest development in the Sea Mar Community Health Center data breach, they’d probably sing:
Third verse, same as the first
A little bit louder and a whole lot worse
Last month, DataBreaches.net reported that Sea Mar Community Health Center in Washington state had been sued in November, weeks after they disclosed a data breach that they had first become aware of in June, 2021. Because the lawsuits were filed in November, the complaints filed mentioned some data had shown up on the dark web. A lot more would show up later, however, and not just on the dark web.
By February, data from Sea Mar had been dumped twice on both the dark web and clear net: some data was dumped by the Marketo group in June, 2021, to entice people to buy or bid on what they claimed was 3 TB of data. Then in January, Snatch Team dumped 22 GB of data from “Private Company #1” that appeared to be Sea Mar’s data. As this site reported, the data dump included a variety of file types and information. As DataBreaches.net reported at the time, “One file alone contained more than 160,000 individuals’ name, date of birth, and SSN. Other files contained their addresses and telephone numbers.” The data were freely available to whoever wanted to download it on both the dark web and on clear net.
As in past attempts to alert them and to get a response from them, Sea Mar did not respond to notification by, or queries by, DataBreaches.net about the 22 GB data dump. This site also alerted the Washington Attorney General’s Office because of the now-increased risk to patients and employees.
But there was more to come, it seems. Snatch Team recently listed “Private Company #2” on its site, and dumped more than 160 GB of data.
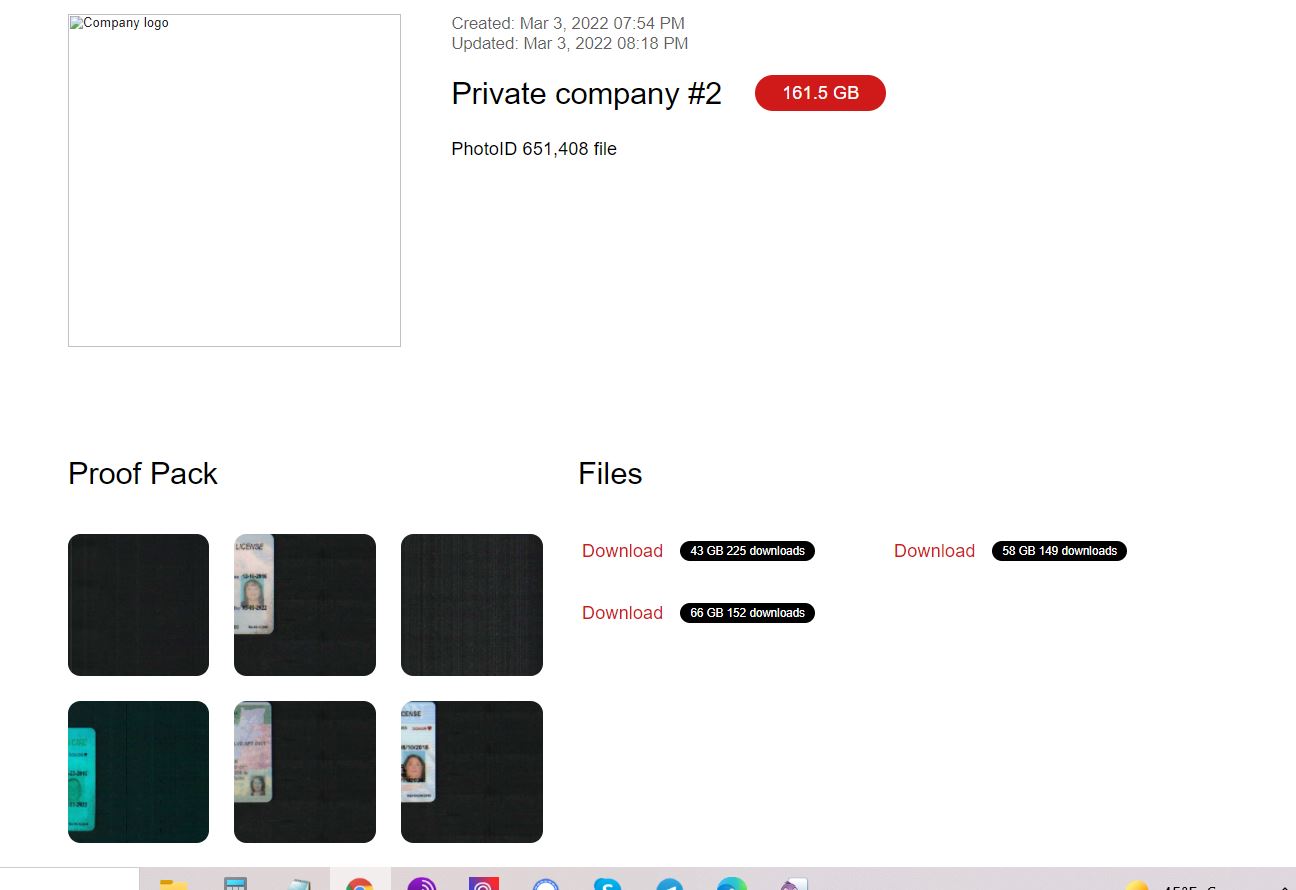
How many of those image files are employees’ drivers’ licenses and how many may be patient-related drivers’ licenses is unknown to DataBreaches.net, but while some of the files are quite old and licenses would be expired, other files are newer. Unlike the 22 GB dump, this newer dump contained only photo IDs like driver’s licenses, but there were more than 650,000 of such files.
As it did with “Private Company #1,” Snatch Team would not confirm that the data were from Sea Mar. In a chat, a spokesperson for Snatch Team informed DataBreaches.net that not all dumps on their site were their work and others posting data to their site did not always indicate the source. In their own words:
We are not a state project. We do not belong to any country, either in whole or in part. We are international, anyone who is registered on our portal can post information about the hacked company. Something we hack ourselves, something is published by our users. Our business model probably simply does not exist, the world is so globalized that to destroy it, missiles or aircraft are no longer needed, but a group of people with certain skills and hacker attacks on critical infrastructure are enough. And our goal is to draw people’s attention to this problem, because those who are responsible for security are absolutely unwilling to recognize the fact that security around the world, information security is 0. As for the Sea Mar campaign, we cannot name it due to the fact that the person who posted it did not indicate the source of the data leak.
But one thing is clear by now: data with PII and PHI of Sea Mar employees and patients has already been leaked on both the dark web and clear net, increasing the risk of misuse. To this site’s knowledge, there has been no updated notice by Sea Mar to alert people to the January and March data dumps with so much information.
Once again, DataBreaches.net reached out to Sea Mar to alert them to this newest leak and to ask them if they had ever notified employees and patients that their information was being shared widely on the internet.
Once again, no reply was received.
Plaintiff’s counsel were asked if they had any comment on the newest leak, but they, too, did not reply.