On June 27, Clarin reported that OSDE had suffered a cyberattack on June 25.
OSDE is a network of medical care services and providers in Argentina. People can enroll in pre-paid health plans and contact OSDE online when they need medical attention or assistance. According to its site, OSDE currently has over 2 million members, more than 8,000 pharmacies, and almost 400 centers for members needing medical or personalized attention in person.
The attack reportedly resulted in OSDE being unavailable online for a few hours.
On June 27, OSDE confirmed the attack, but without confirming it was a ransomware incident.
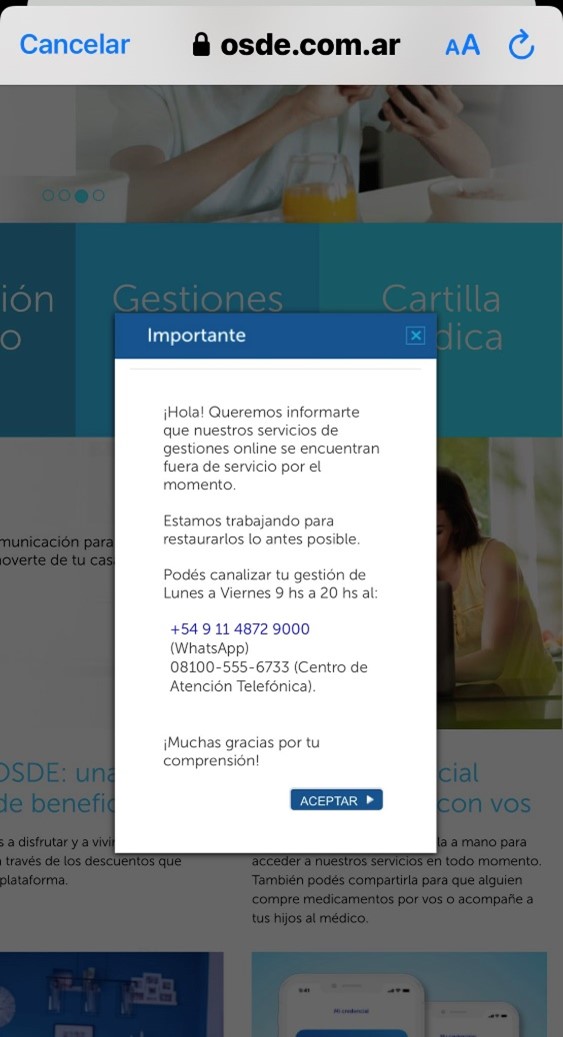
Machine translation of notice on OSDE’s site reads, in part: “Hello! We would like to inform you that our online management services are out of service for the moment. We are working to restore them as soon as possible.”
Email inquiries to OSDE on June 26 by DataBreaches seeking clarification on how services were being affected went unanswered.
Because Clarin reported that some sources suggested that LockBit was responsible for the attack, DataBreaches also reached out to LockBit on June 30 to ask if they were responsible for the attack.
“Can you tell me if that’s true? Is OSDE a LockBit victim?” they were asked.
LockBitSupp responded, “idk” (“I don’t know”).
Time Passes and LockBit Suddenly Knows
On July 22, LockBit added OSDE to their dedicated leak site on the dark web with a price tag of $300,000 to purchase or remove all the data, a proof pack (sample of files), and a deadline of August 6.

DataBreaches reached out to LockBit again on July 25 to determine how much personal or sensitive information Lockbit had exfiltrated about employees, affiliates, and members. They never answered that inquiry by August 8, when they dumped what they claim was 139.07 GB of files.
DataBreaches also reached out to OSDE again on July 25 to repeat inquiries about whether the attack affected functions or patient care, but again, got no reply.

Inspection of files in the leak revealed folders with names of people who appear to be affiliates of OSDE, audit-related files, billing and collection-related files, taxes, and “rescues. The “rescue” folder had subfolders for 2020, 2021, and 2022, and affiliate-related files. Some of these files involved Binaria Seguros, a life insurance company owned by OSDE. Many of the folders listed in the file-tree were empty.

All in all, DataBreaches saw very little personal information in the files that were reviewed, and no real patient data. (SEE CORRECTION AND UPDATE BELOW)
So what in this data leak could possibly be worth $300,000? As far as DataBreaches has seen, this leak is mostly a big nothing.
DataBreaches sent one more email to OSDE asking them if LockBit acquired any patient data, if it acquired any personal or sensitive employee or affiliate information, and if it notified any patients, employees or affiliates, or the data protection regulator. Other than an auto-responder to acknowledge receipt, no reply was received.
Editing by Dissent.
If anyone receives a notification of the breach from OSDE or has additional information indicating that personal and sensitive information was accessed or acquired, please email [email protected].
CORRECTION AND UPDATE: A threat analyst, Mauro Eldritch, who reviewed all the data informed Clarin that he found sensitive information:
…. there are files that refer to fragments of medical records, medical studies, patient lists, PCR test results and absolutely private and intimate medical information, such as serious diseases and treatments.
Regarding the affected users, the expert said: “Scanned copies of DNI, data and procedures of Politically Exposed Persons (PEP) were leaked, including politicians, journalists and celebrities, as well as their relatives.
Read more at Clarin.