Nonstop Health offers health insurance solutions to employers who have more than 50 employees receiving benefits. Headquartered in Concord, California, and Portland, Oregon, Nonstop Health has business associate agreements with its clients that covers protected health information.
On January 17 and 18, data and source code allegedly from Nonstop were leaked on two popular hacking-related forums.
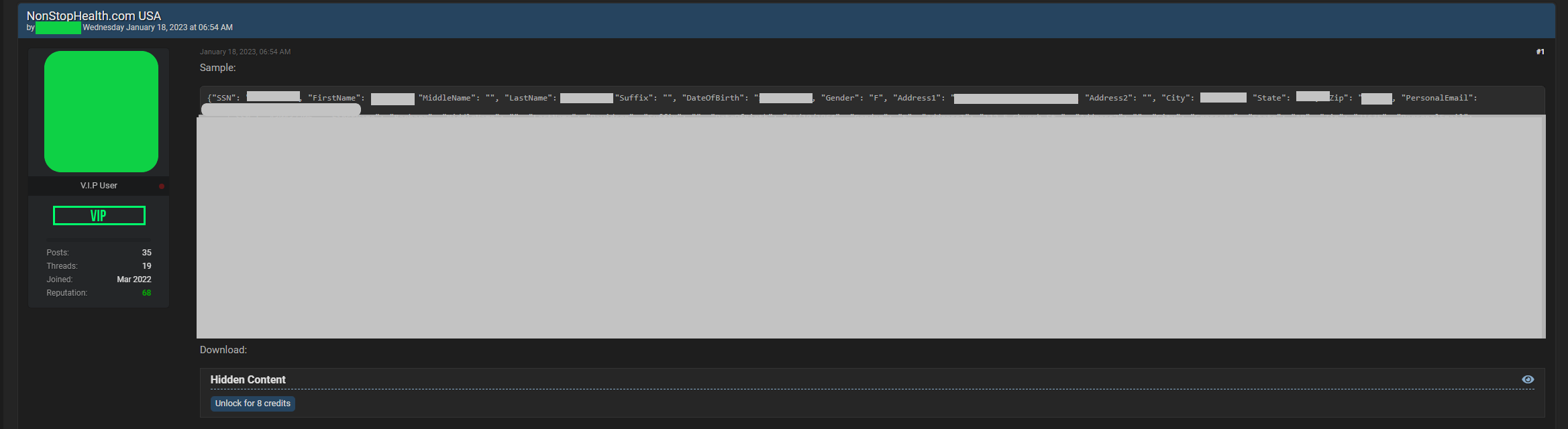
Personal information leaked online included names, date of birth, postal address with state and zip code, personal email address, and Social Security numbers. For some records, cellphone number, employee status, job title, and annual salary were also included. Given the formatting of the sample data, the sample appears to have been drawn from a number of clients’ data and not just one. The full leak by the poster reportedly contains 43,532 lines and the data are reportedly from December, 2022.
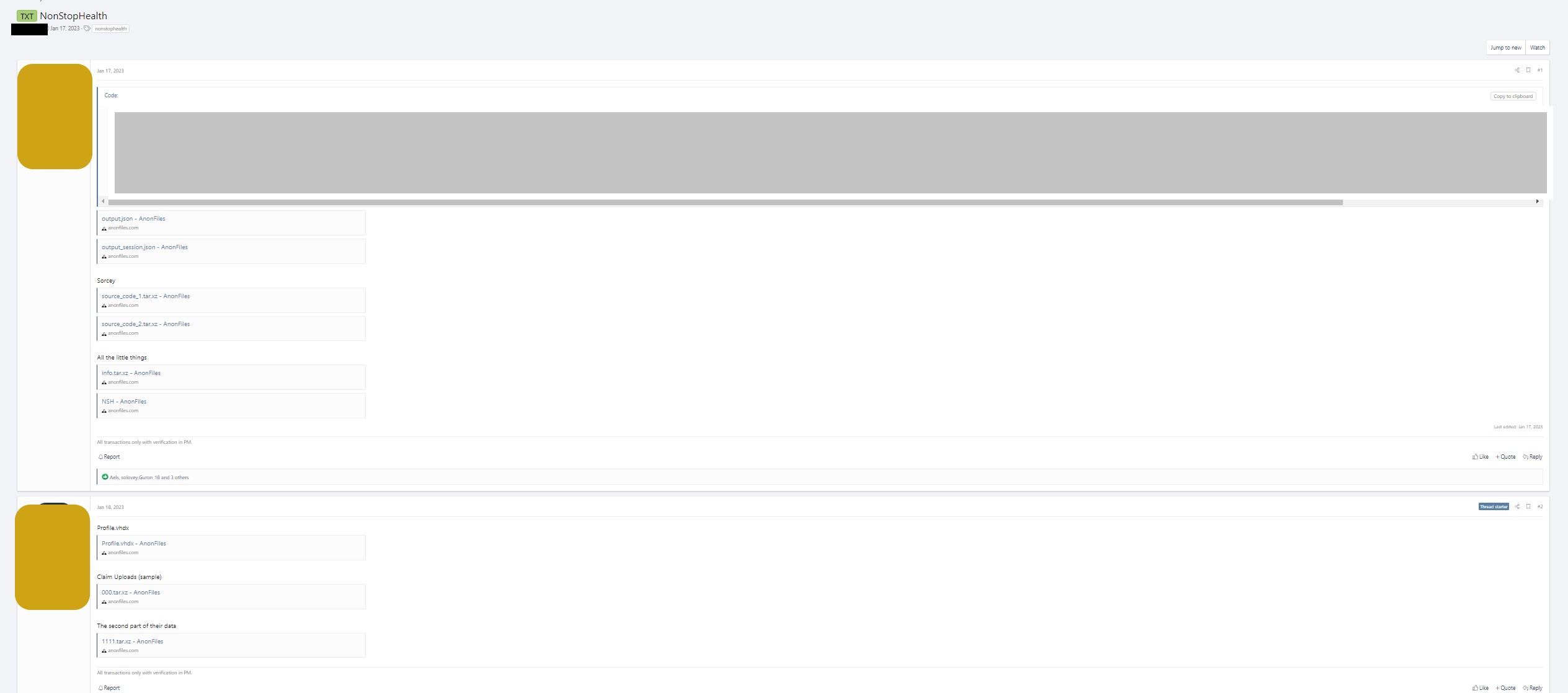
The same data had been previously posted on a popular Russian-language forum with source code files:
Since January 19, DataBreaches has reached out to Nonstop Health on multiple occasions to ask them for a response to the leak or situation, but despite a few auto-replies acknowledging the inquiries and saying there would be a response in 24-48 hours, there has been no real response. On January 29, DataBreaches sent email inquiries to three individuals whose data appeared in the sample. Inquiries were sent to one of the forum listers on January 24 and January 29.
Because the forum user has not replied with any additional information, it is not yet clear or confirmed how access was gained to the data and whether the user tried to negotiate any ransom payment with Nonstop Health or not. Nor is it known yet whether Nonstop Health has notified any of its clients or their employees whose personal information appears to now be in an adversary’s hands.
DataBreaches will update this post if more information becomes available.
Updated June 2, 2023: In February, Nonstop notified Indiana that 796 patients were affected. In March, Nonstop notified HHS that 8,571 patients had been affected, but it is not clear on whose behalf they were reporting. The same month, they notified the Maine Attorney General’s Office on behalf of Mat-Su Health Services,that 462 patients were affected. On May 26, Nonstop notified the California Attorney General’s Office of the breach on behalf of Eisner Health. The notification letter dated February 15, 2023 made no mention that any data had already been leaked in January on at least two forums, noted above.