LockBit has added White Settlement Independent School District in Texas to their leak site, with a proof pack that suggests that the threat actors were able to access — and may have exfiltrated — a lot of files. The listing was added yesterday.
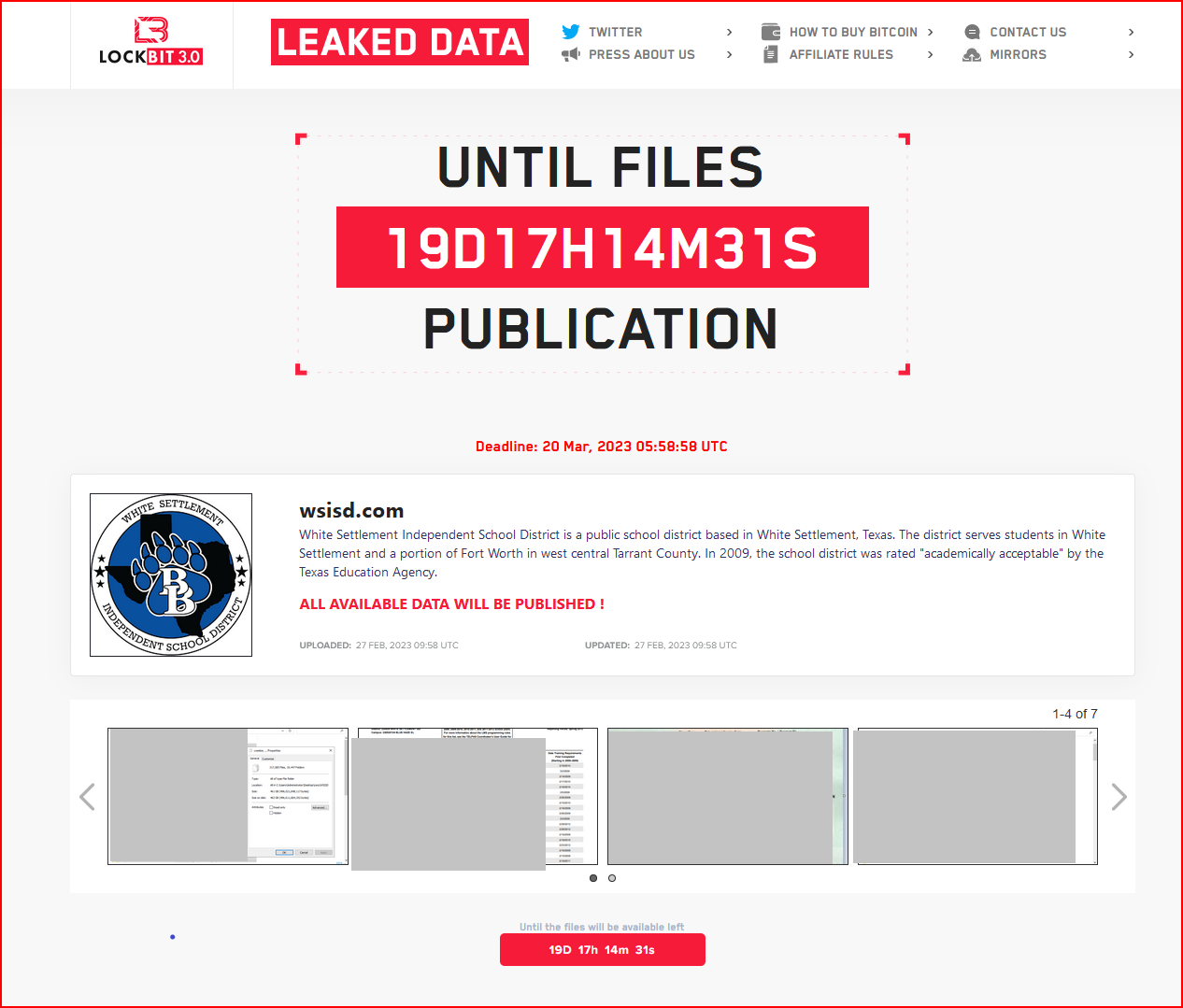
There is no notice on WSISD’s website that DataBreaches could find about any incident or cyberattack, and it’s not known if any files were encrypted or if this was an attack in which data were just exfiltrated for ransom or extortion purposes. None of the files in the proof pack are demonstrably recent files, and a number of them have dates suggesting that they are from 2015 or earlier. One file, however, had an image of a passport issued in 2020.
DataBreaches has sent an inquiry to the district about the claimed attack and will update this post if a reply is received.
Update: The following statement was sent to the district’s staff and families. A copy was sent to DataBreaches by Desiree Coyle, White Settlement ISD Communications Director:
White Settlement ISD was recently informed by Homeland Security that the district experienced a possible cyberattack. District officials immediately began security intrusion prevention. Upon further investigation and security scans, WSISD determined that Skyward/Gradebook and Canvas were not compromised. The district discovered that the only compromised documents belonged to some staff members and were housed in a shared folder.
Prior to this incident, WSISD had taken numerous cybersecurity measures to protect student and staff data. In the event that the district finds that your information was compromised, district officials will contact you. We will continue to work closely with several agencies to ensure that there are no future vulnerabilities.
Students and staff members who have concerns about their data being compromised should follow the recommendations from identitytheft.gov<https://www.identitytheft.gov/#/Steps>.
That description — that “the only compromised documents belonged to some staff members and were housed in a shared folder,” does not sound like any kind of a large breach. If LockBit leaks more data, we may find out how accurate the district’s statement is.