Montana State University was hit with a cyberattack on April 20. They are still working to recover from it. Here is their latest update:
Campus network update: NetID password changes, service status page
Sent at 8:18 a.m. Friday, April 28, via email to students, faculty and staff.
As work continues to return Montana State University’s services to normal operation, University Information Technology (UIT) wishes to remind all NetID users to reset their passwords by visiting the Self-Service Password Portal at http://password.montana.edu. Please note, any passwords that have not been changed by the end of the day will be reset automatically.
Additionally, starting today, you can view the status of MSU services on a new web page. A link to the Services Status page is posted prominently at https://www.montana.edu/communications/april2023cyberincident. To view the page, you will need to log in with your NetID.
UIT is updating the Services Status page on an ongoing basis. If you have a question about a service that is not listed there, send an email to [email protected].
Thank you for your patience and cooperation.
No mention of ransomware?
Threat and Risk Intelligence Services pointed out to DataBreaches that the university’s update does not mention that this is a ransomware attack by Royal that has been listed on Royal’s leak site (but without data as yet).
Royal’s listing ominously claims to have acquired 105GB of files.
“Students’ personal and medical information is also available like in our previous post about their affiliated college. We will share it soon,” Royal claims in their April 29 listing.

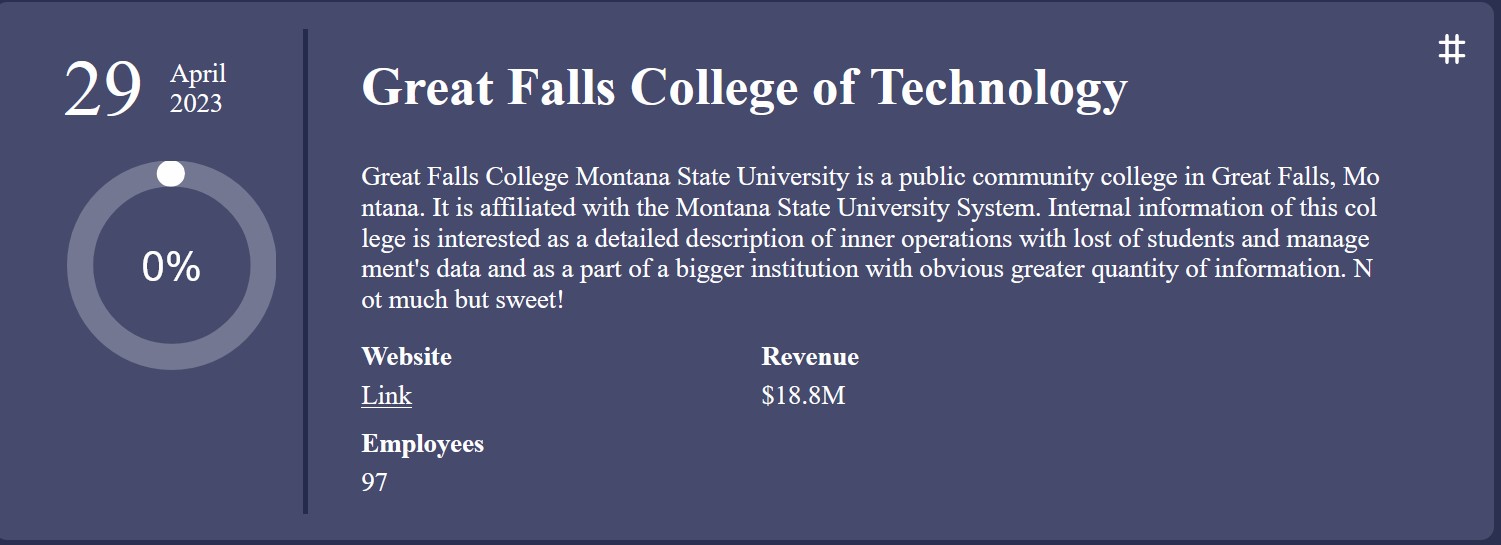
The reference to the “affiliated college” concerns the Great Falls College of Technology, which has also been listed on Royal’s leak site without any data as yet. Royal claims to have acquired 20GB of data from the college that they describe as, “Not much, but sweet!”
Perhaps the university has issued some other notice elsewhere that alerts employees and students about the claimed theft of their personal and sensitive information. Hopefully, they have.