On April 22, the Murfreesboro Medical Clinic in Tennessee suffered a ransomware attack that resulted in them having to shut down all operations on May 1-3 to limit the spread of the attack. The clinic’s statement was previously reported on DataBreaches.net.
A notice on their website today advises patients that MMC Pediatrics has resumed normal weekend operations but MMC Now Family Walk-In Clinics and laboratory and radiology services remain closed. MMC staff will be contacting patients over the weekend to confirm appointments and surgeries for Monday. Previous updates can be found on their site on a special Alerts page.
Attacked by BianLian?
Although the clinic has not identified the threat actors, DataBreaches was able to identify BianLian as the threat actor based on an obfuscated listing on their leak site with a matching number of asterisks for the name of the victim as well as information about the number of patients seen by the clinic each month and its revenue as reported on zoominfo.com.
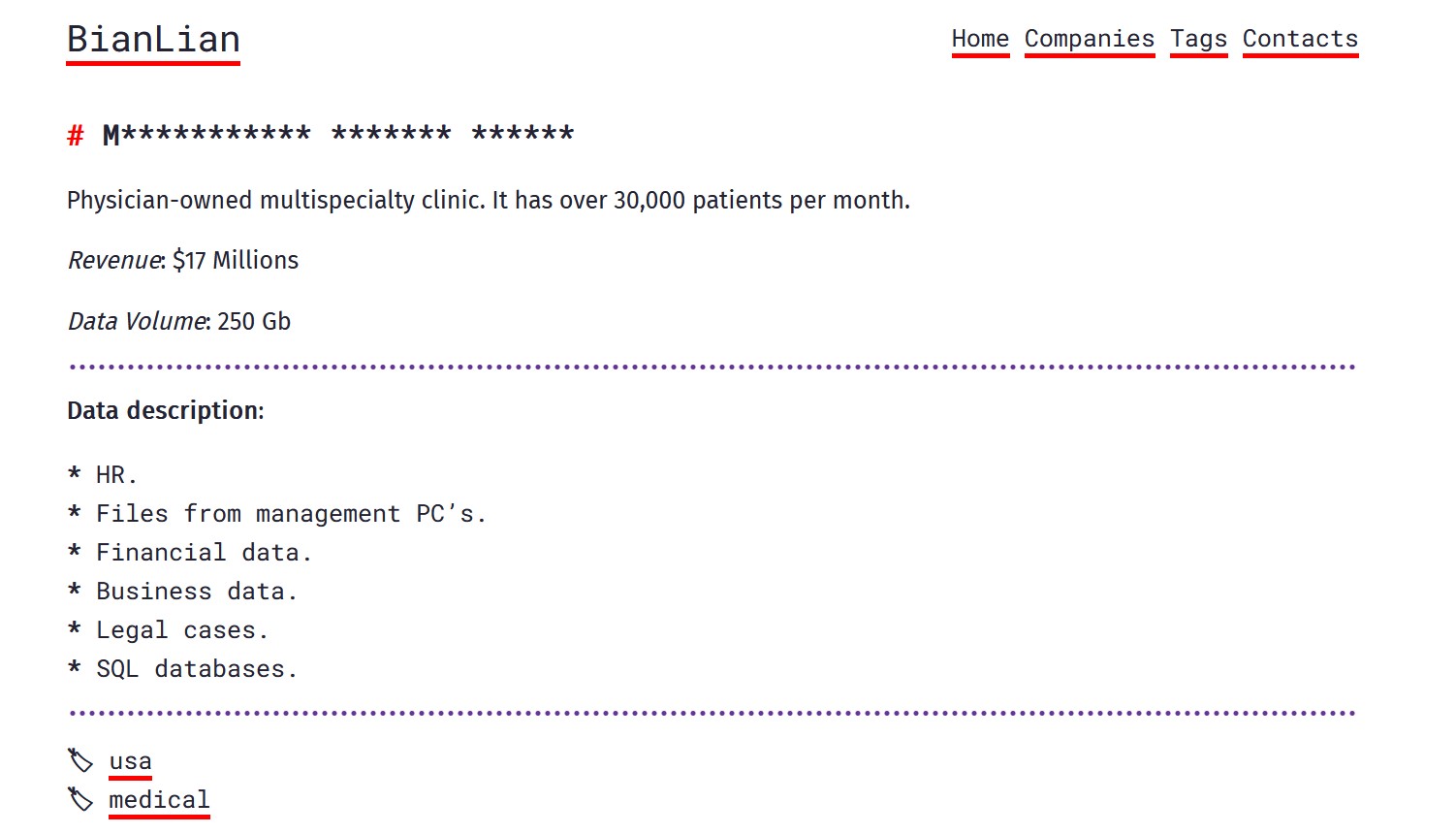
BianLian claims to have 250GB of files from their victim.
Given the clinic reports that they are swamped with calls, DataBreaches has not reached out to them to ask them to confirm this site’s attribution.