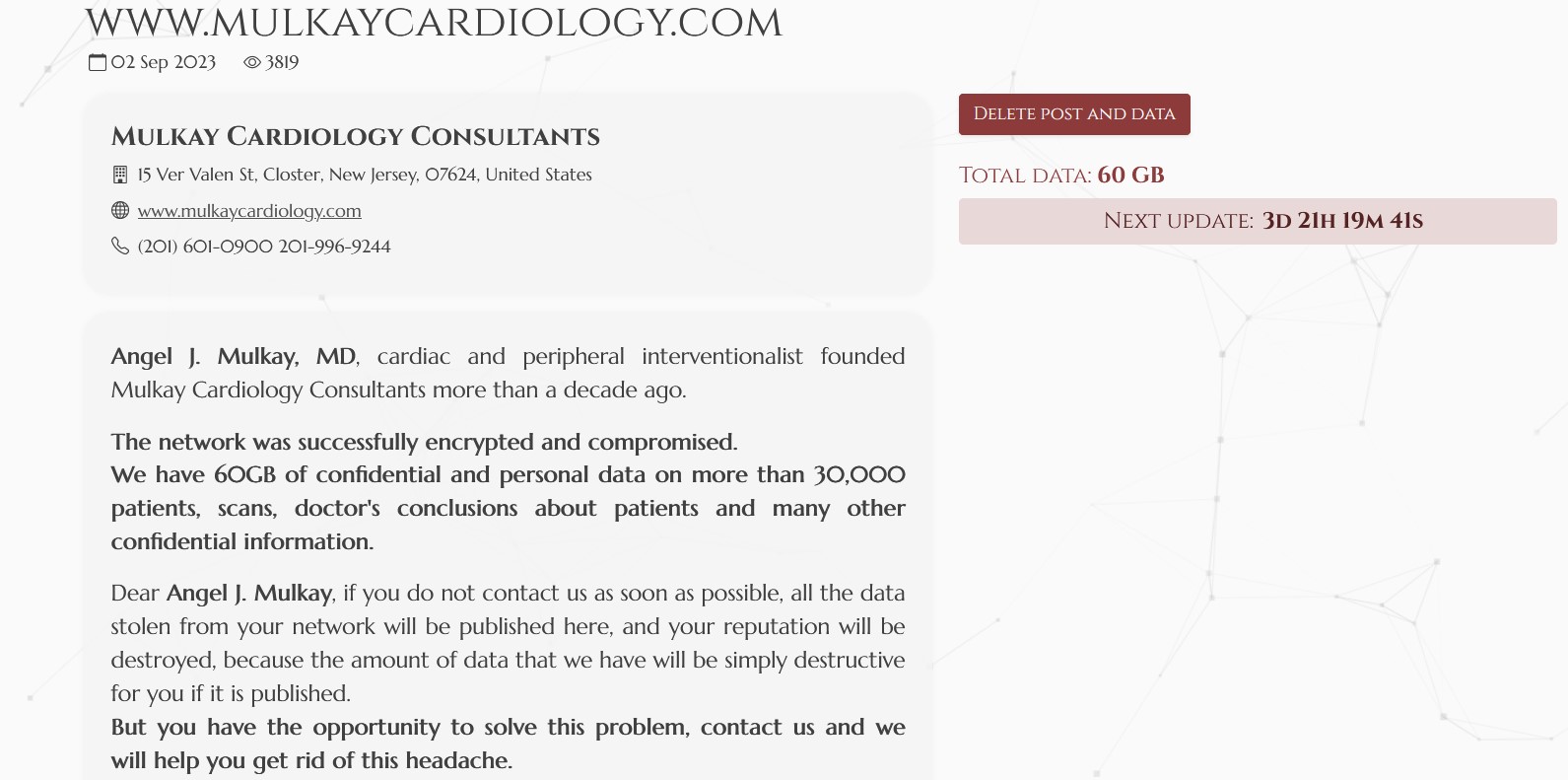
On September 2, the NoEscape ransomware group added Mulkay Cardiology Consultants to their leak site and claimed to have successfully encrypted them.
“We have 60GB of confidential and personal data on more than 30,000 patients, scans, doctor’s conclusions about patients and many other confidential information,” they claimed in their listing about the New Jersey medical practice.
DataBreaches checked Mulkay’s website at the time and found nothing amiss and no email address or contact form to use to contact them. DataBreaches reached out to NoEscape via their contact form to request some proof of claims, but received no reply.
On September 19, DataBreaches noticed that NoEscape had added a “DDoS” label to the Mulkay listing and to several other victims’ listings. Attempts to connect to Mulkay’s site returned a 508 error (resource limit reached).
On re-check today, Mulkay’s website is reachable, and there is no alert or notice on it to indicate any breach or issue.
Of note, the Mulkay listing on NoEscape’s leak site could not be found there today. DataBreaches sent an inquiry earlier today to NoEscape asking about its removal but received no reply.
Did Mulkay pay, or was the listing removed because they started to negotiate, or is there some other reason? DataBreaches will continue to try to find out about the alleged attack.