In November 2024, Everest Team added Concord Orthopaedics (“COPA”) to its dark web leak site (DLS) with screenshots offered as proof of claims. At the time, Everest claimed to have acquired “medical records and personal data of all patients from 2018. More than 30,000 identity documents.”
On March 25, 2025, COPA mailed notifications to those affected, and their counsel notified the New Hampshire Attorney General’s Office about the incident.
According to their notification, on November 21, 2024,COPA learned that a vendor who handles their patient registration and appointment check-in software was breached. They do not name the vendor but say that COPA’s own internal environment was not affected at all. The types of information accessed or acquired from the vendor’s software included:
- Name
- Date of birth
- Social Security number
- Appointment Information: The information captured by the third-party software is limited to information related to the appointment, such as appointment type (for example, surgical, MRI, etc.), treating physician name, and date and location of appointment
- Health Insurance Information: This may include health plan beneficiary number, health plan number, and insurance eligibility information. Some of this information may belong to the primary insurance holder.
- Driver’s License or State Identification Number: For a portion of the population, an image of your driver’s license or state identification card may be impacted.
On January 28, 2025, the third-party vendor provided COPA with the data potentially impacted.
According to the notification to New Hampshire by Troutman Pepper Locke, 67,835 New Hampshire residents were affected by the incident. The total number of patients was not reported, and as of publication, no listing has shown up on HHS’s public breach tool for incidents affecting more than 500 patients.
But as COPA announced it was mailing out letters, Everest was announcing that it had leaked the data from COPA. The data tranche was 2.9 GB of files.
Update 1: This incident was also reported to the Massachusetts Attorney General’s Office as affecting 1,517 Massachusetts residents.
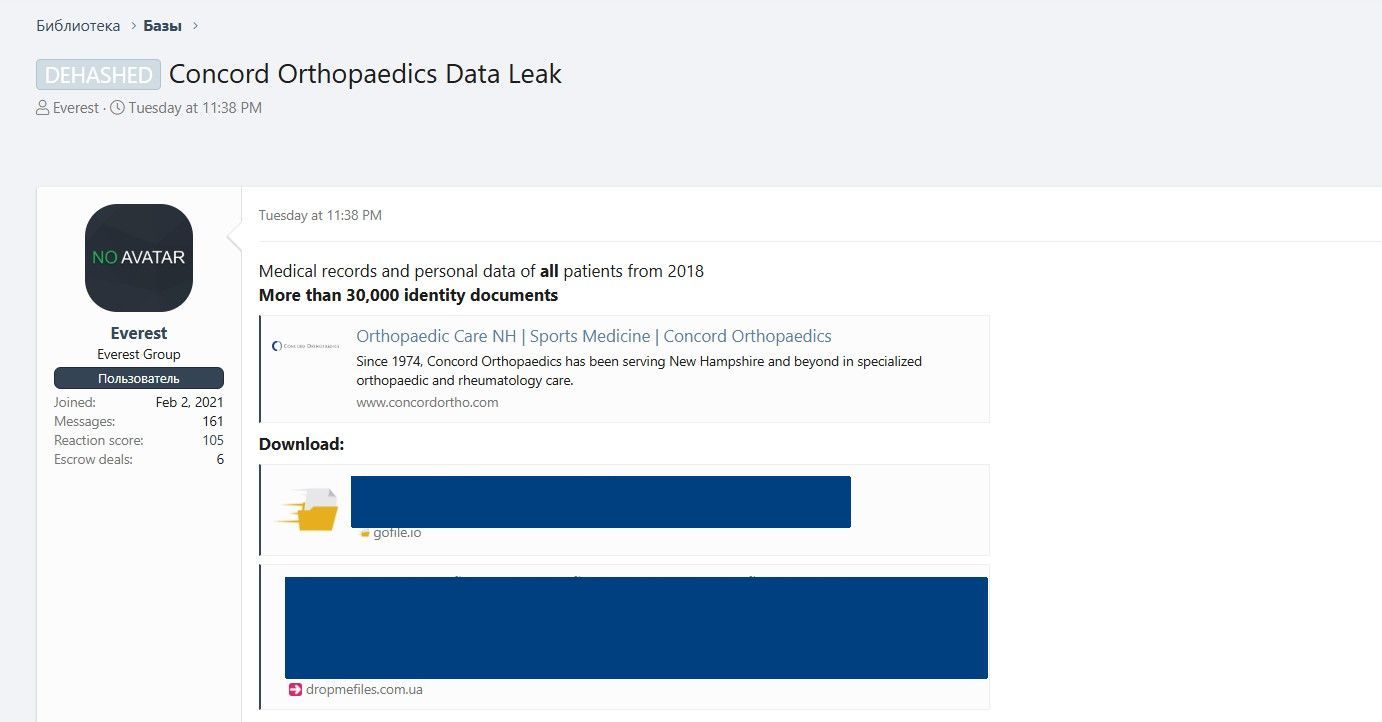
Everest’s description of the data tranche was somewhat incomplete. DataBreaches did find one file with more than 30,000 images of driver’s licenses, but there were other files in .csv format with a wealth of personal and protected health information on patients seen between 2019-2024. This leak involved much more than patients seen in 2018.
Why the unnamed vendor stored so much unencrypted PII and PHI on their server is unknown to DataBreaches.